Issue
- You receive a notification about a certificate being expired, revoked, unsigned, or otherwise invalid
- SSL/TLS protocol filtering and root certificates
- ESET certificate notifications
- Non-ESET certificate notifications
Solution
SSL/TLS protocol filtering and root certificates
SSL/TLS protocol filtering allows ESET home and small office products for Windows to scan for threats in communications that use the SSL/TLS protocols. SSL/TLS protocol filtering is enabled by default in all ESET home and small office products for Windows.
We recommend keeping this setting enabled to ensure that your ESET security product provides you with the maximum level of protection. To disable or re-enable SSL/TLS protocol filtering for troubleshooting purposes, manage SSL/TLS protocol filtering.
When SSL/TLS protocol filtering is enabled, your ESET security product adds an ESET root certificate to your local machine. The ESET root certificate is trusted and valid, and allows your product to scan SSL traffic to verify if other certificates are also trusted and valid. If your product detects an untrusted or invalid certificate, we will alert you with one of several notifications. For more information, see the SSL/TLS Online Help topic.
You can find detailed information about specific notifications ESET home and small office products below.
ESET certificate notifications
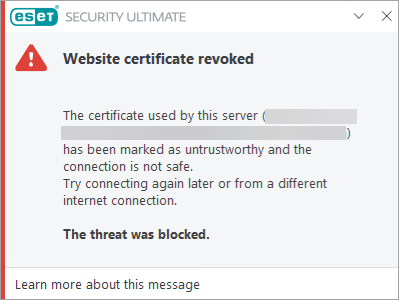
Website certificate revoked
This notification alerts you that the security certificate for a website is expired, the issuing Certificate Authority has revoked the security certificate, or the issuing Certificate Authority itself has been revoked.
Read more about Website certificate revoked notification.
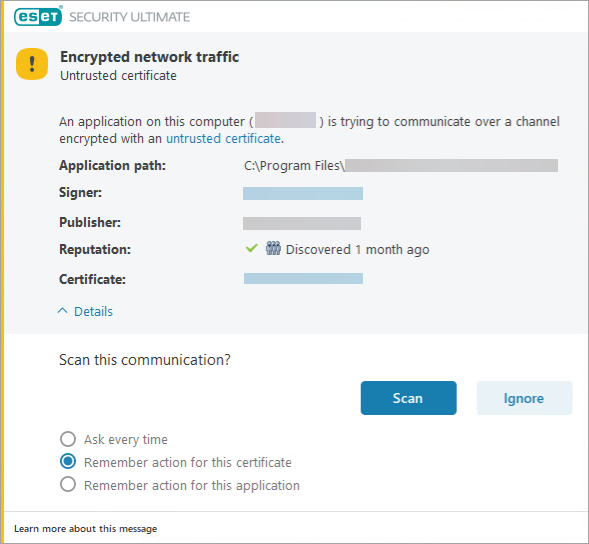
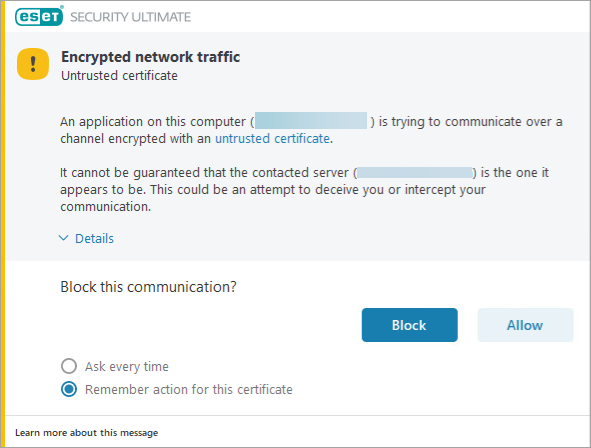
Encrypted network traffic: Untrusted certificate
This notification alerts you that a certain app is trying to communicate over a channel encrypted with an untrusted certificate. You may also receive this notification when an ad with an invalid certificate tries to load on a website.
Notification appearance might be different based on the product settings.
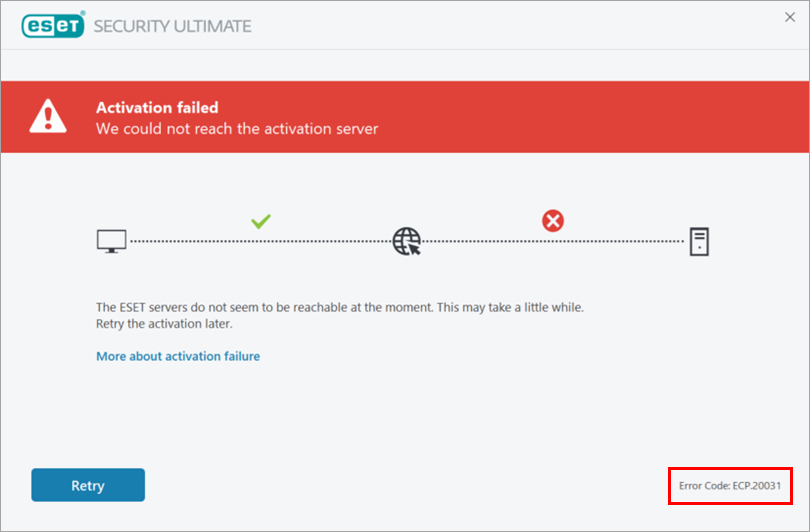
Activation failed / Error Code: ECP.20031
This notification alerts you that outdated or insufficient security certificates were encountered during your ESET security product installation.
You can find the Error Code in the bottom right corner of the product window.
Read more about the certificate validation failure during installation or activation of ESET products.
Non-ESET certificate notifications
Connection is untrusted / sec_error_reused_issuer_and_serial error message
These notifications come from your browser rather than your ESET security product.
Verify that you have SSL/TLS protocol filtering enabled in your security product.