Issue
- File-level scanning of some email servers, backup software, Customer Relationship Management (CRM) software, etc. causes abnormal system behavior
- Use ESET Configuration Editor to create a configuration that excludes specific applications or folders from Real-time scanning
- Add Performance exclusions by editing the endpoint policy
- Add Detection exclusions from the Detections tab and managed from the Exclusions tab
Solution
![]() Endpoint users: Perform these steps on individual client workstations
Endpoint users: Perform these steps on individual client workstations
Add a Performance exclusion
-
Click Policies, select your desired policy for client computers and click Edit.
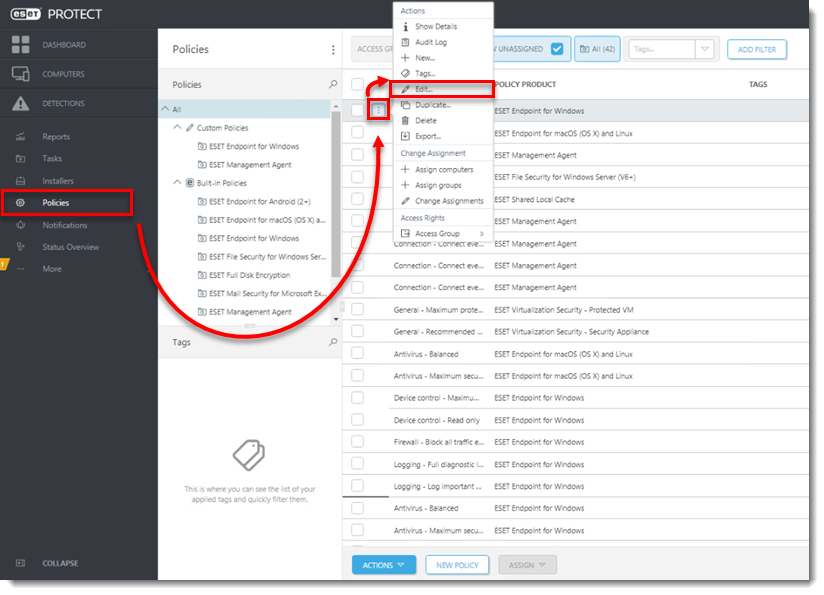
Figure 1-1
-
Click Settings → Detection Engine, expand Exclusions, and then click Edit next to Performance exclusions.
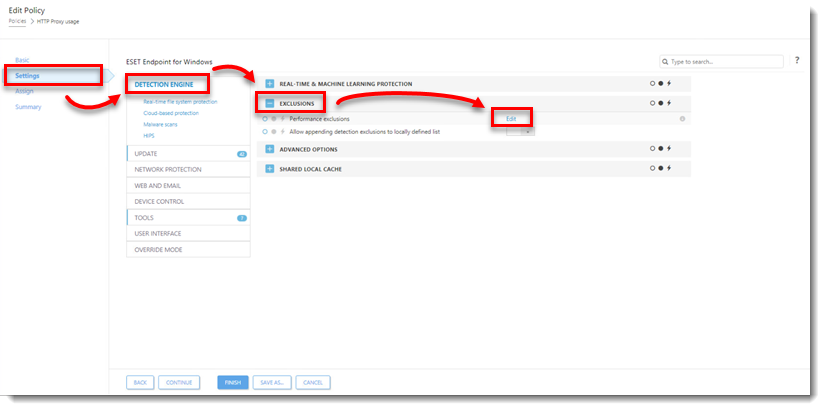
Figure 1-2 -
Click Add, type the directory that you want to exclude from scanning into the Path field and add a comment for the exclusion in the Comment field. Click OK. Make sure the file path for your exclusion is in the correct format, for example, "
C:\Users\[username]\Documents\file.exe".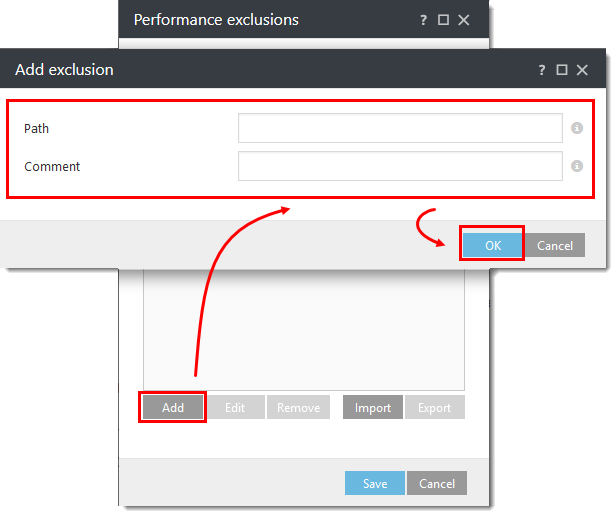
Figure 1-3
-
Click Save when you are finished adding exclusions.
-
Click Finish to save your changes.
Add a Detection exclusion
-
Click the Detections icon and then click the detection you want to exclude.
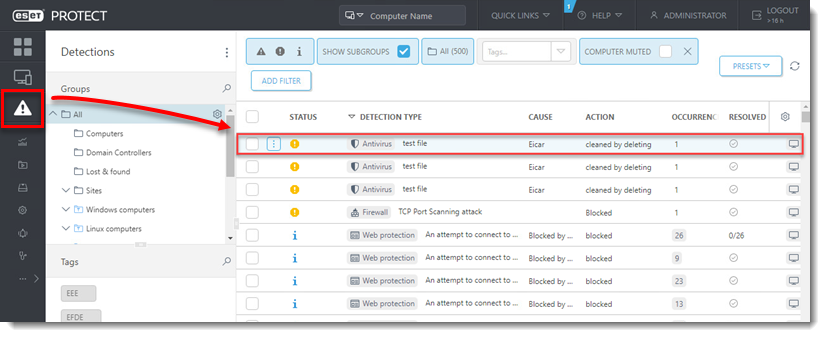
Figure 2-1
-
Select Create Exclusion.
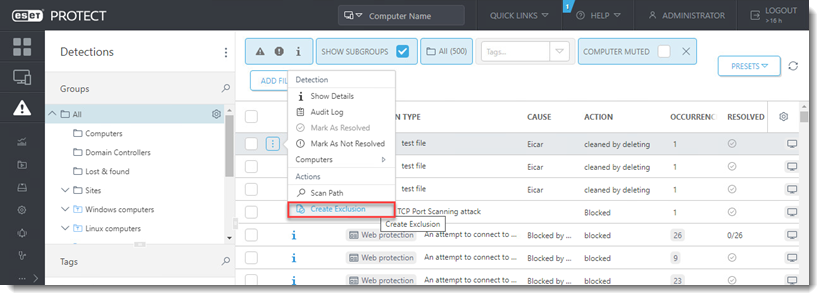
Figure 2-2
-
Select the desired Exclusion criteria and click Add. Visit our online help topic for more information about Exclusion criteria.
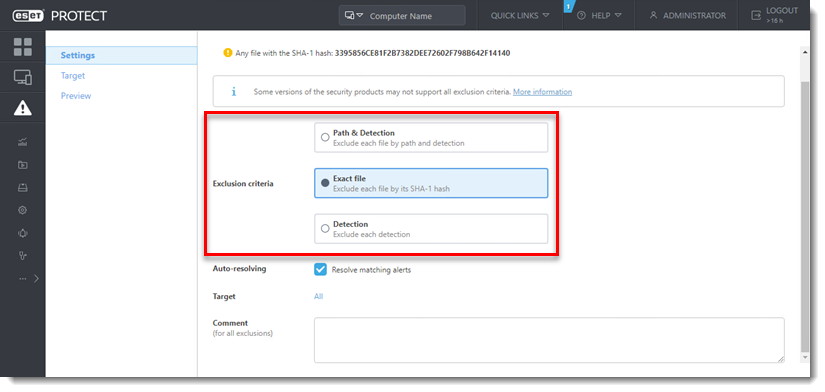
Figure 2-3
-
Click More (...) → Exclusions to manage the Detection exclusion.
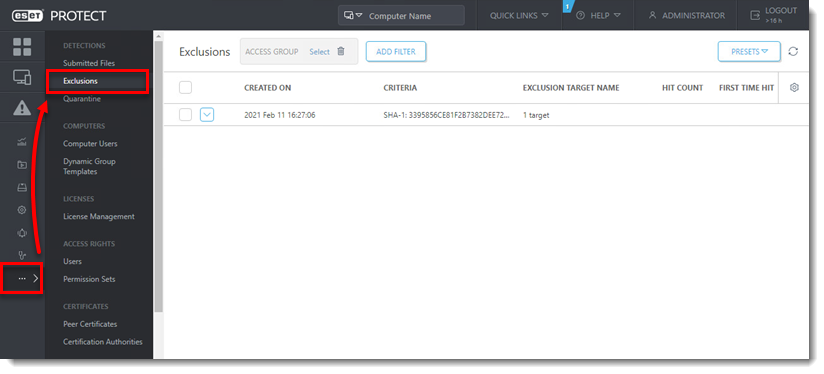
Figure 2-4