Issue
- Use Jamf Pro to deploy version 7 of ESET Endpoint Antivirus for macOS on macOS Sonoma (14)
- If you have upgraded to macOS Sequoia (15), see Deploy ESET Endpoint Security for macOS using Jamf Pro
- Troubleshooting issues after using Jamf Pro to upgrade to ESET Endpoint Security for macOS version 8
Solution
Follow the instructions below to deploy your ESET Endpoint Security product for macOS using Jamf Pro to manage using ESET PROTECT or ESET PROTECT On-Prem.
- Configure System Extensions, Privacy Preference Policy Control (PPPC), VPN, and Content Filter profile
- Create Policies
- Additional Options
I. Configure System Extensions, PPPC, VPN, and Content Filter profile
- Open Jamf Pro and click Computers → Configuration Profiles to set the approval for System Extensions, PPPC, VPN, and Content Filter and click New to add a new configuration profile (one configuration profile can contain all the settings).
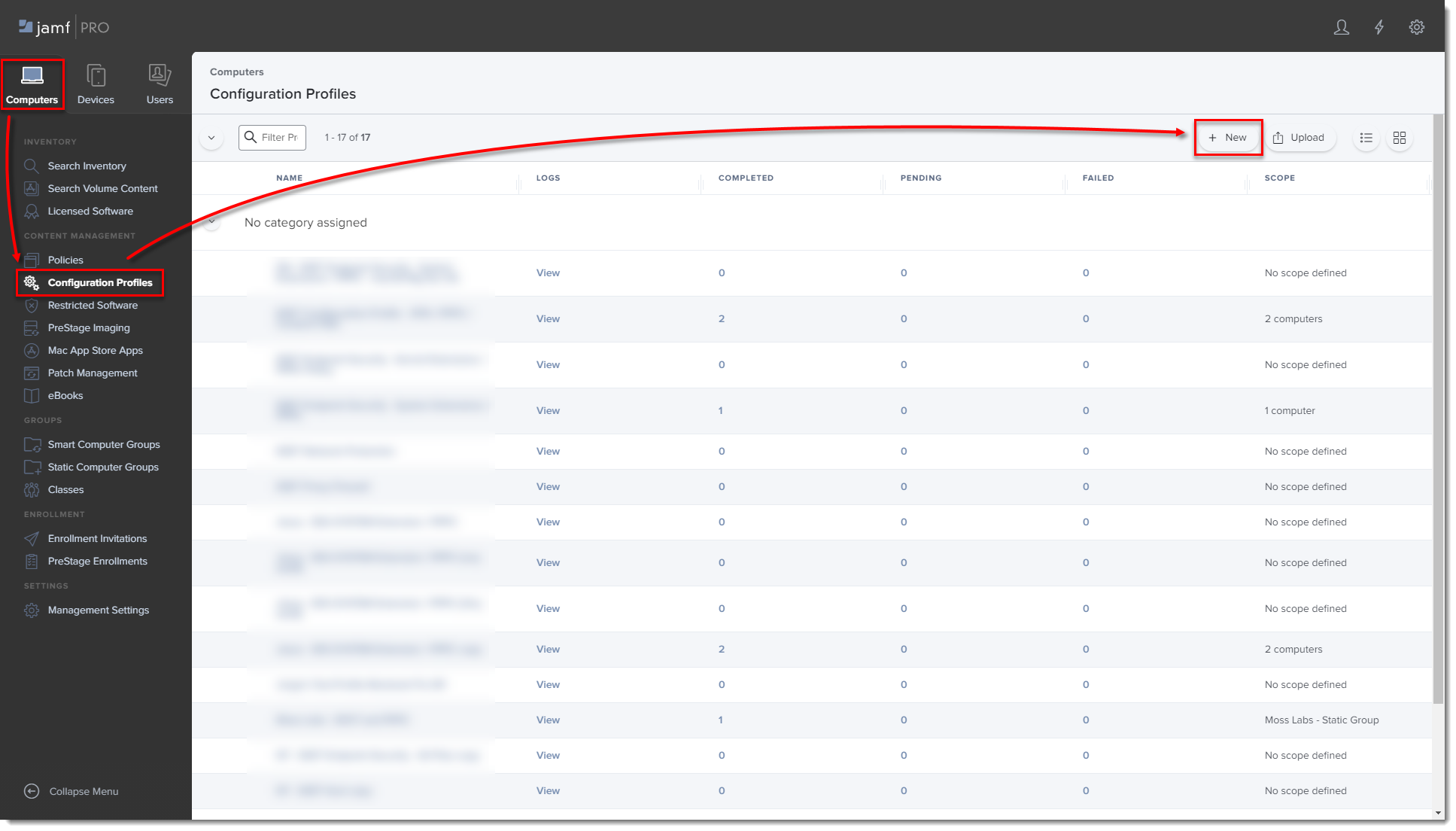
Figure 1-1
Click the image to view larger in new window
-
Type a Name for the profile.
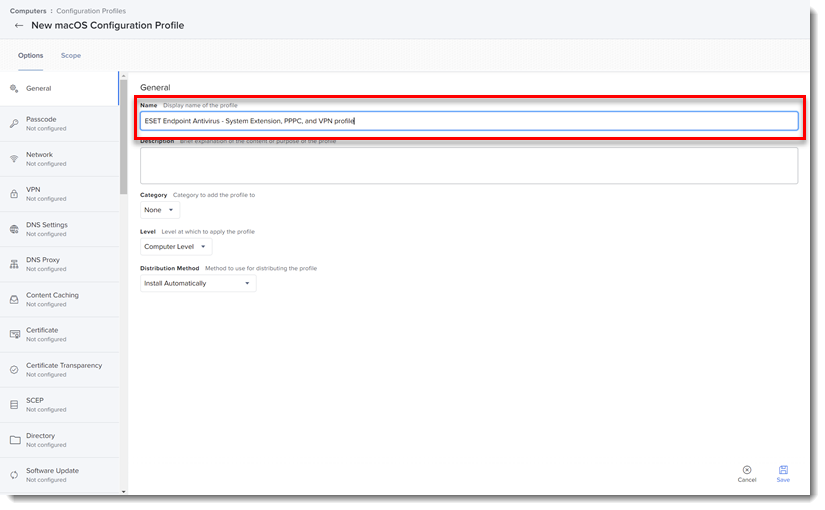
Figure 1-2
-
In the Options tab, click System Extensions → Configure.
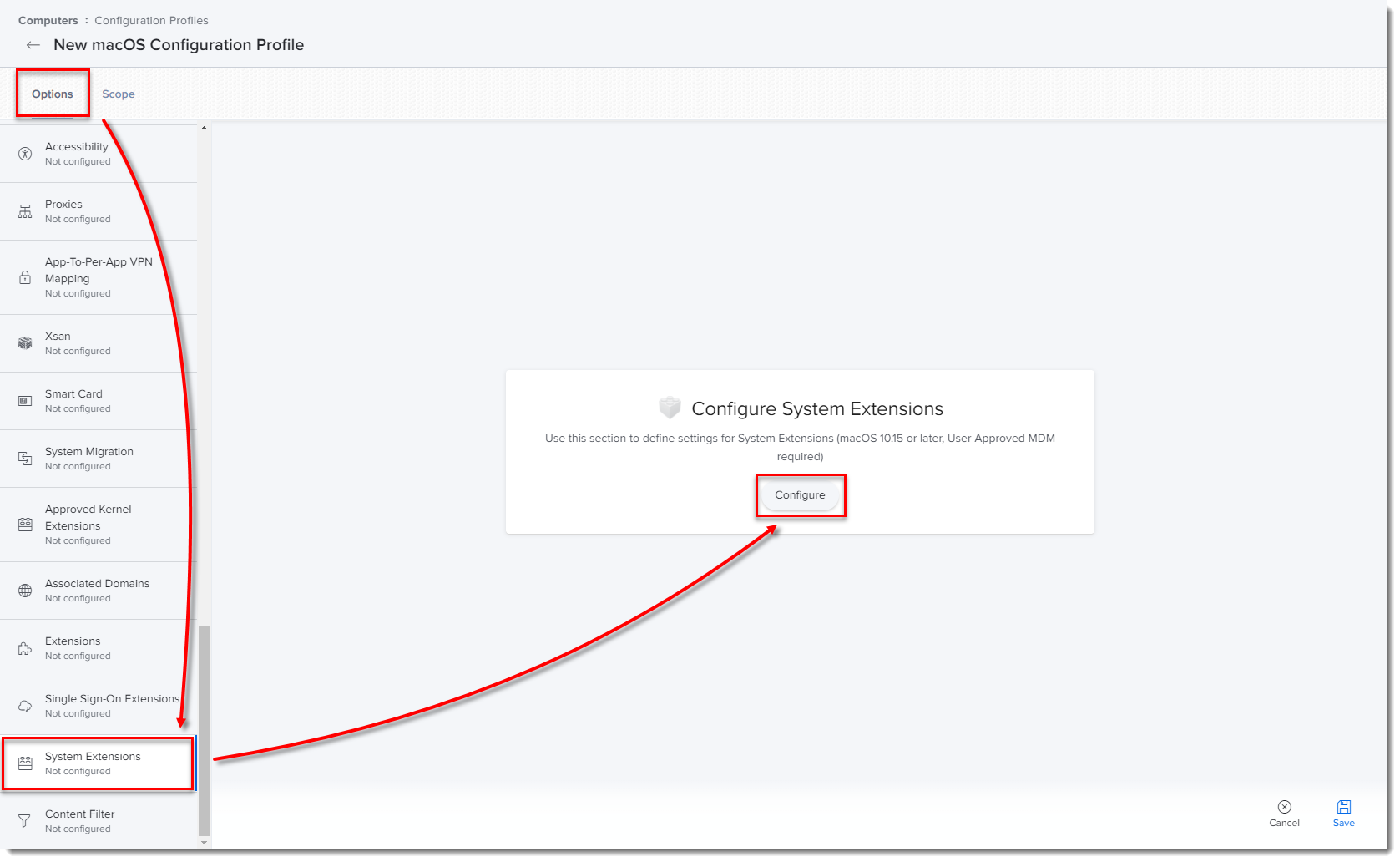
Figure 1-3
Click the image to view larger in new window -
In the Allowed TEAM IDs and System Extensions section, type the following information:
- Display Name: ESET SE [you can choose any name you want]
- System Extension Types: Allowed System Extensions
- Team Identifier: P8DQRXPVLP
- Allowed System Extensions:
com.eset.endpoint
com.eset.network
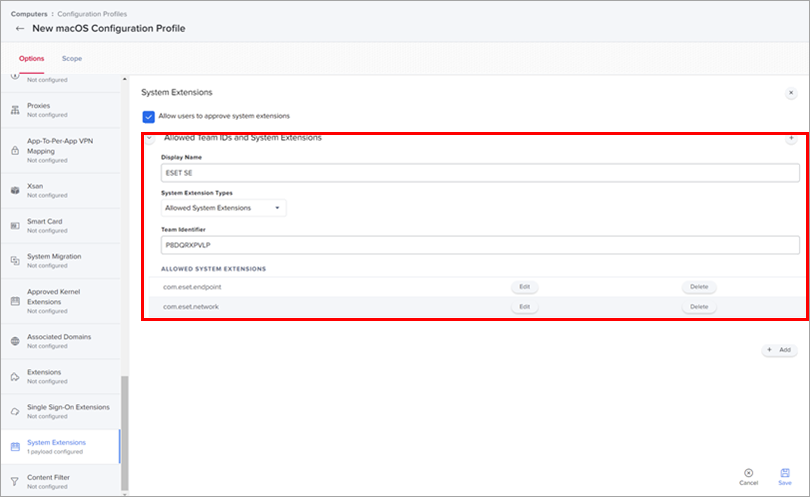
Figure 1-4
Click the image to view larger in new window -
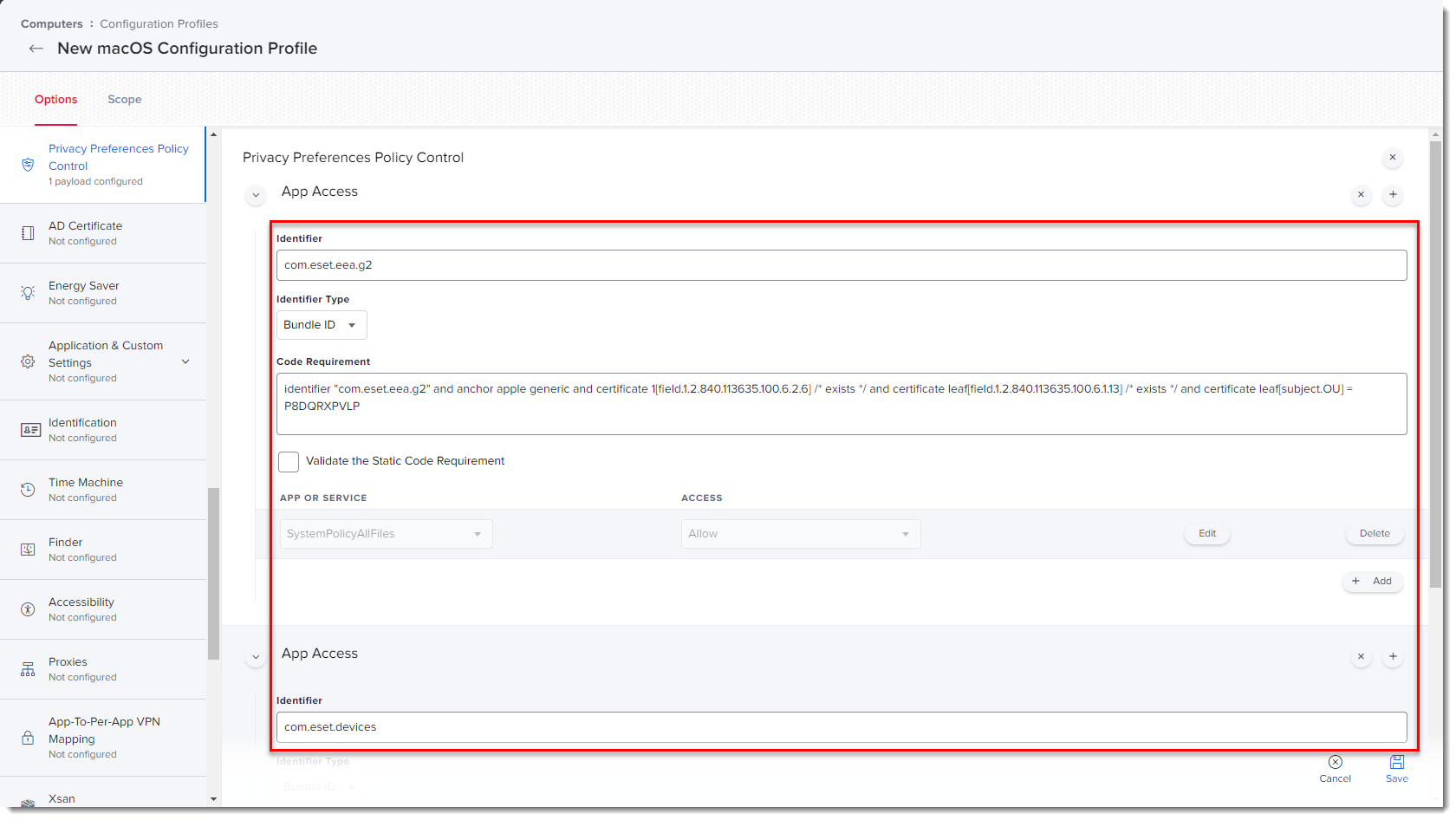
In the Options tab, click Privacy Preferences Policy Control → Configure.
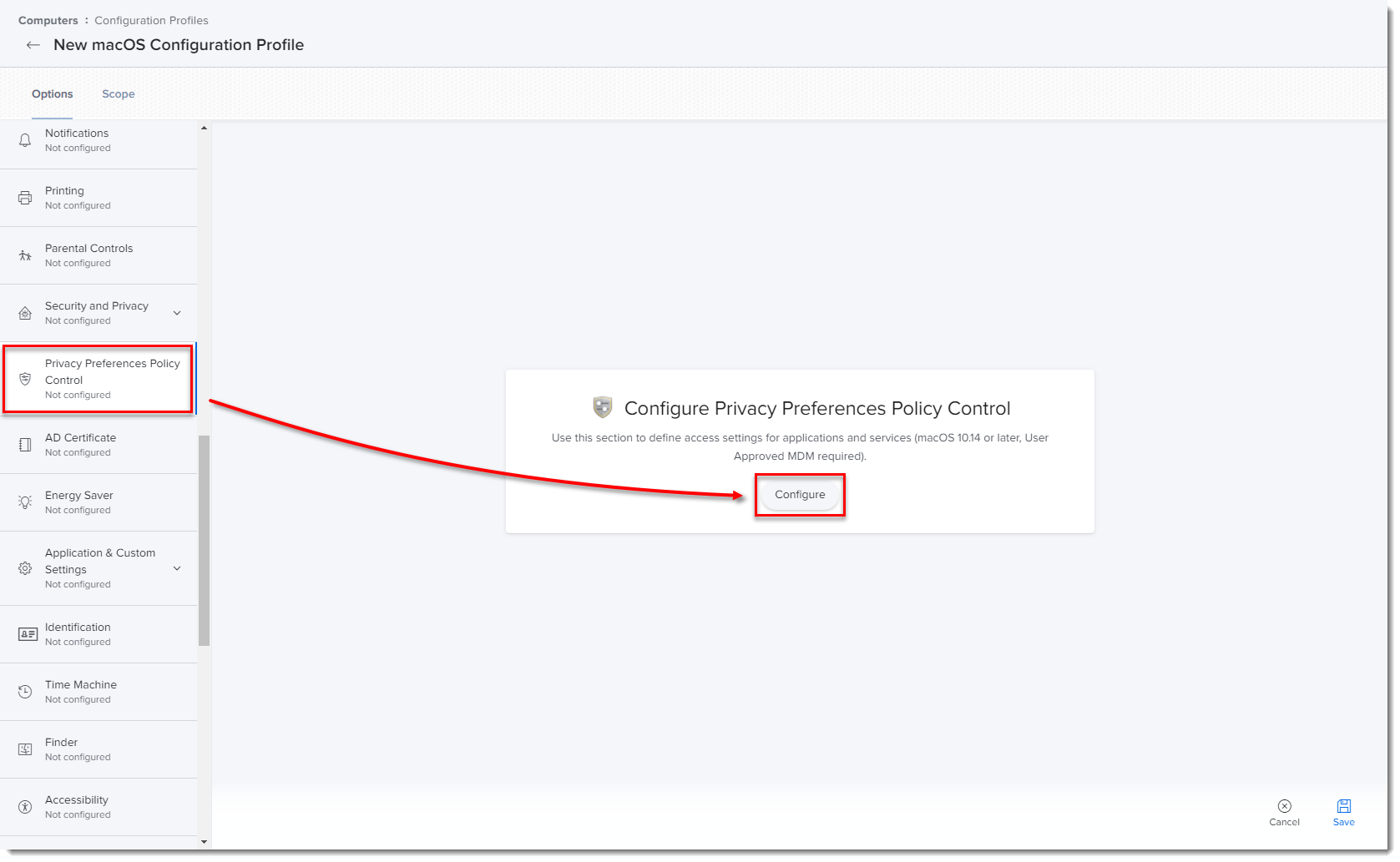
Figure 1-5
Click the image to view larger in new window
Add in the following information for your applicable ESET product:
ESET Endpoint Antivirus for macOS
-
Main product identifier EEA:
-
Identifier: com.eset.eea.g2
-
Identifier Type: Bundle ID
-
Code Requirement:
identifier "com.eset.eea.g2" and anchor apple generic and certificate 1[field.1.2.840.113635.100.6.2.6] /* exists */ and certificate leaf[field.1.2.840.113635.100.6.1.13] /* exists */ and certificate leaf[subject.OU] = P8DQRXPVLP -
App or Service: SystemPolicyAllFiles
-
Access: Allow
-
-
Device identifier:
-
Identifier: com.eset.devices
-
Identifier Type: Bundle ID
-
Code Requirement:
identifier "com.eset.devices" and anchor apple generic and certificate 1[field.1.2.840.113635.100.6.2.6] /* exists */ and certificate leaf[field.1.2.840.113635.100.6.1.13] /* exists */ and certificate leaf[subject.OU] = P8DQRXPVLP -
App or Service: SystemPolicyAllFiles
-
Access: Allow
-
-
Realtime identifier:
-
Identifier: com.eset.endpoint
-
Identifier Type: Bundle ID
-
Code Requirement:
identifier "com.eset.endpoint" and anchor apple generic and certificate 1[field.1.2.840.113635.100.6.2.6] /* exists */ and certificate leaf[field.1.2.840.113635.100.6.1.13] /* exists */ and certificate leaf[subject.OU] = P8DQRXPVLP -
App or Service: SystemPolicyAllFiles
-
Access: Allow
-
Click the image to view larger in new window
-
In the Options tab, click VPN → Configure.
-
Create a configuration profile for ESET Web and Email Protection with the following settings:
- VPN type: VPN
- Connection type: Custom SSL
- Identifier: com.eset.network.manager
- Server: localhost
- Provider Bundle Identifier: com.eset.network
- User authentication: certificate
- Provider Type: App-proxy
- Provider Designated Requirement:
identifier "com.eset.network" and anchor apple generic and certificate 1[field.1.2.840.113635.100.6.2.6] /* exists */ and certificate leaf[field.1.2.840.113635.100.6.1.13] /* exists */ and certificate leaf[subject.OU] = P8DQRXPVLP Select the check box next to Enable VPN on Demand- On Demand Rules Configuration XML:
<array><dict><key>Action</key><string>Connect</string></dict></array> - Idle Timer: Do not disconnect
For more information, see the Online Help guide.
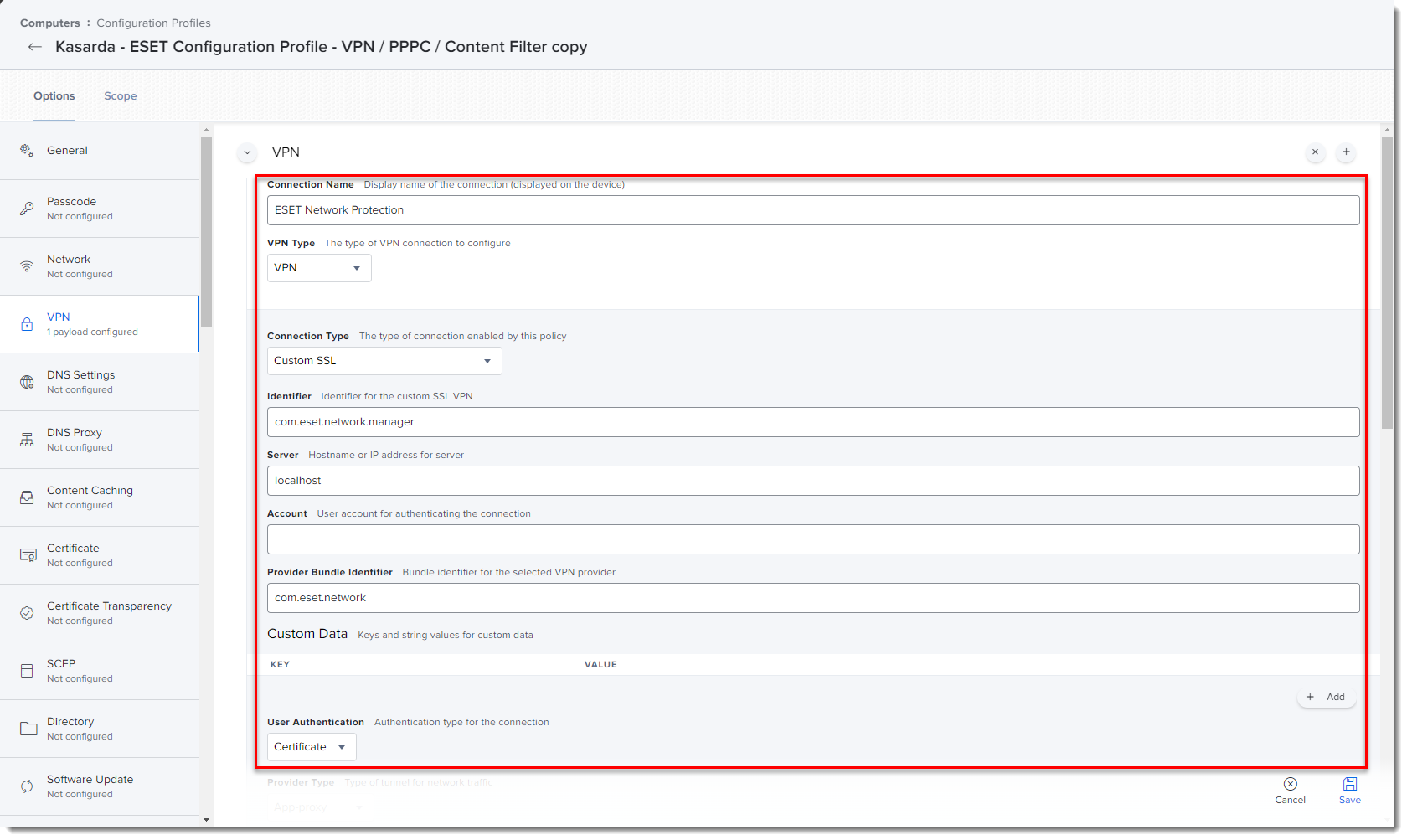
Figure 1-7
Click the image to view larger in new window -
Click the Scope tab and click Add.
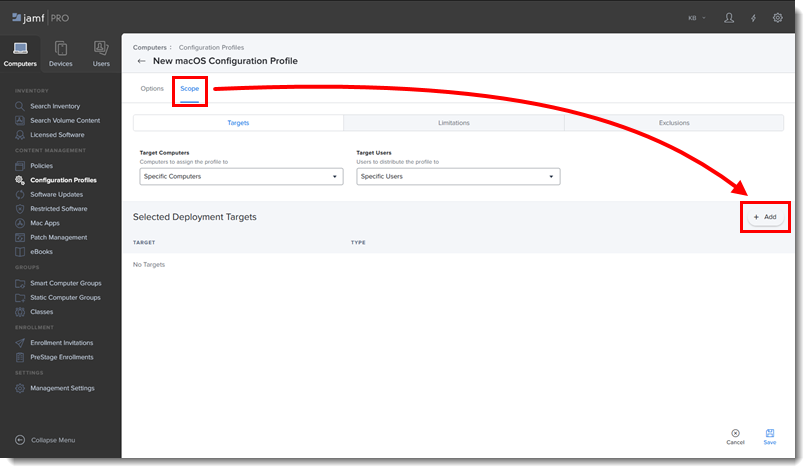
Figure 1-8 -
In the Add Deployment Targets section, select the computers (or Computer Groups) you want to apply the policy to by clicking Add, and then click Done.
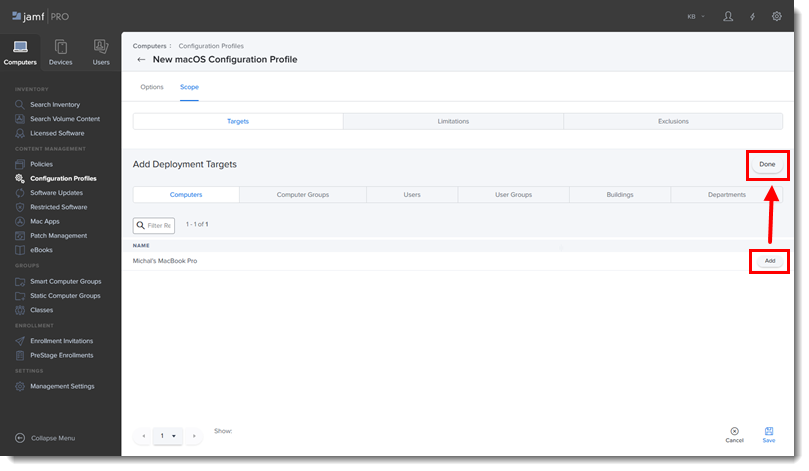
Figure 1-9 -
Click Save to apply your changes.
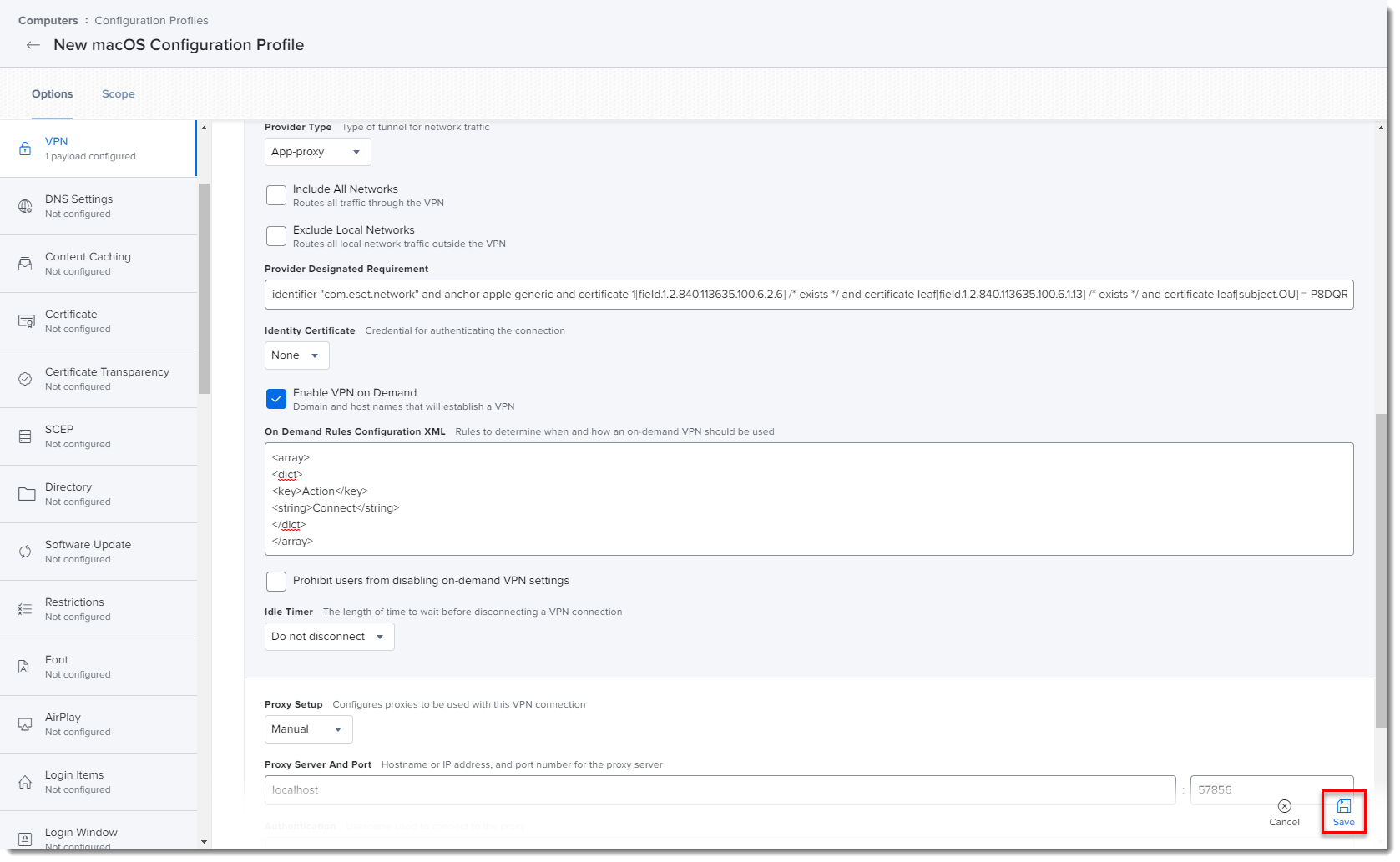
Figure 1-10
Click the image to view larger in new window
II. Create policies
-
Click Policies in the left menu and click New.
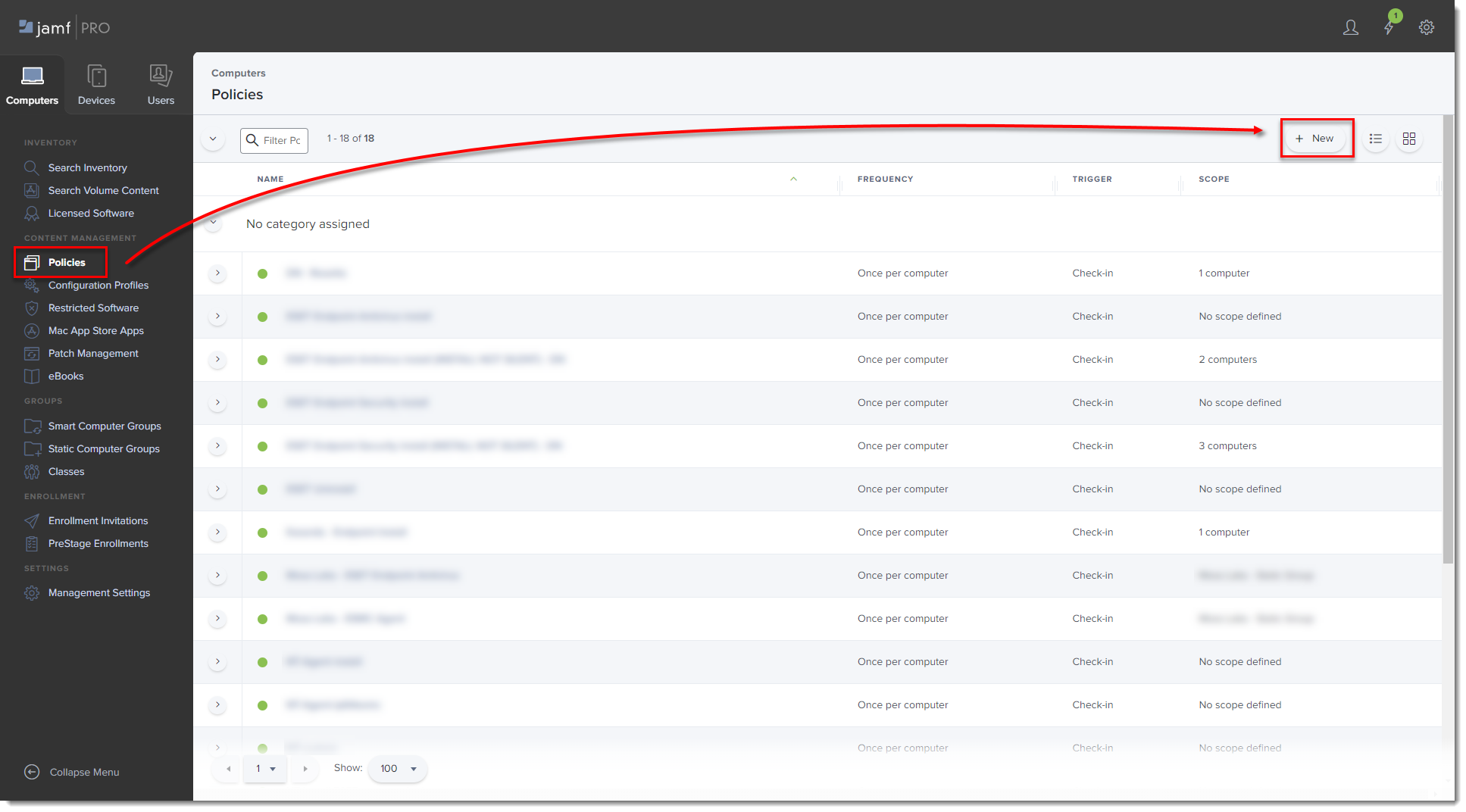
Figure 2-1
Click the image to view larger in new window -
Type a Display Name for the policy, and in the Trigger section, select the Recurring Check-in check box.
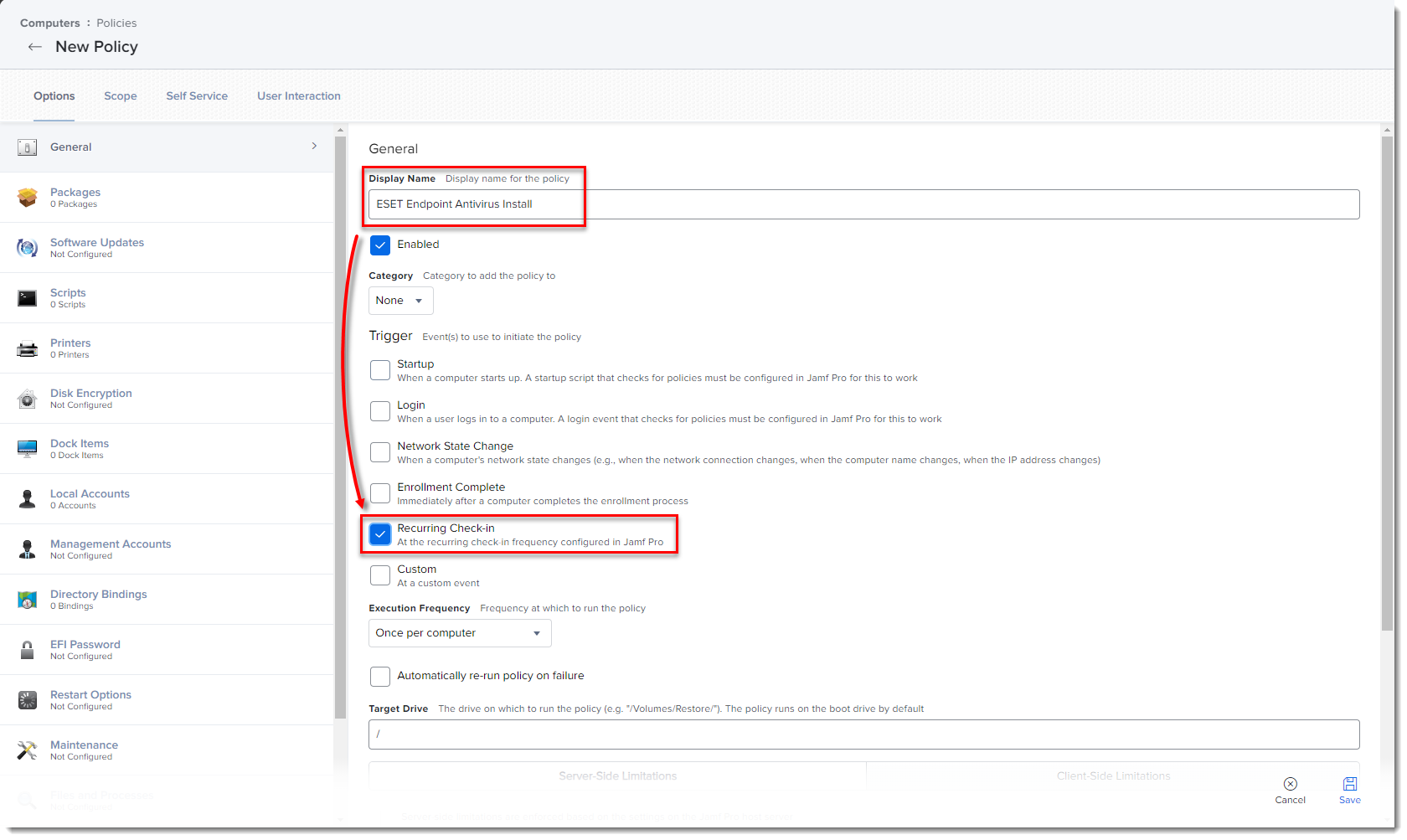
Figure 2-2
Click the image to view larger in new window -
Download the following ESET Security product and ESET Management Agent installation scripts:
- ESET Security product installation script: ESETavJamf_g2.sh (right-click and select Save link as)
- ESET Management Agent installation script: Create the Agent Live Installer and download the PROTECTAgentinstaller.sh file from ESET PROTECT On-Prem.
-
After downloading the scripts, follow the steps in Jamf Pro Administrator's Guide to add the scripts to Jamf.
-
From the Options tab, click Scripts and then click Configure.
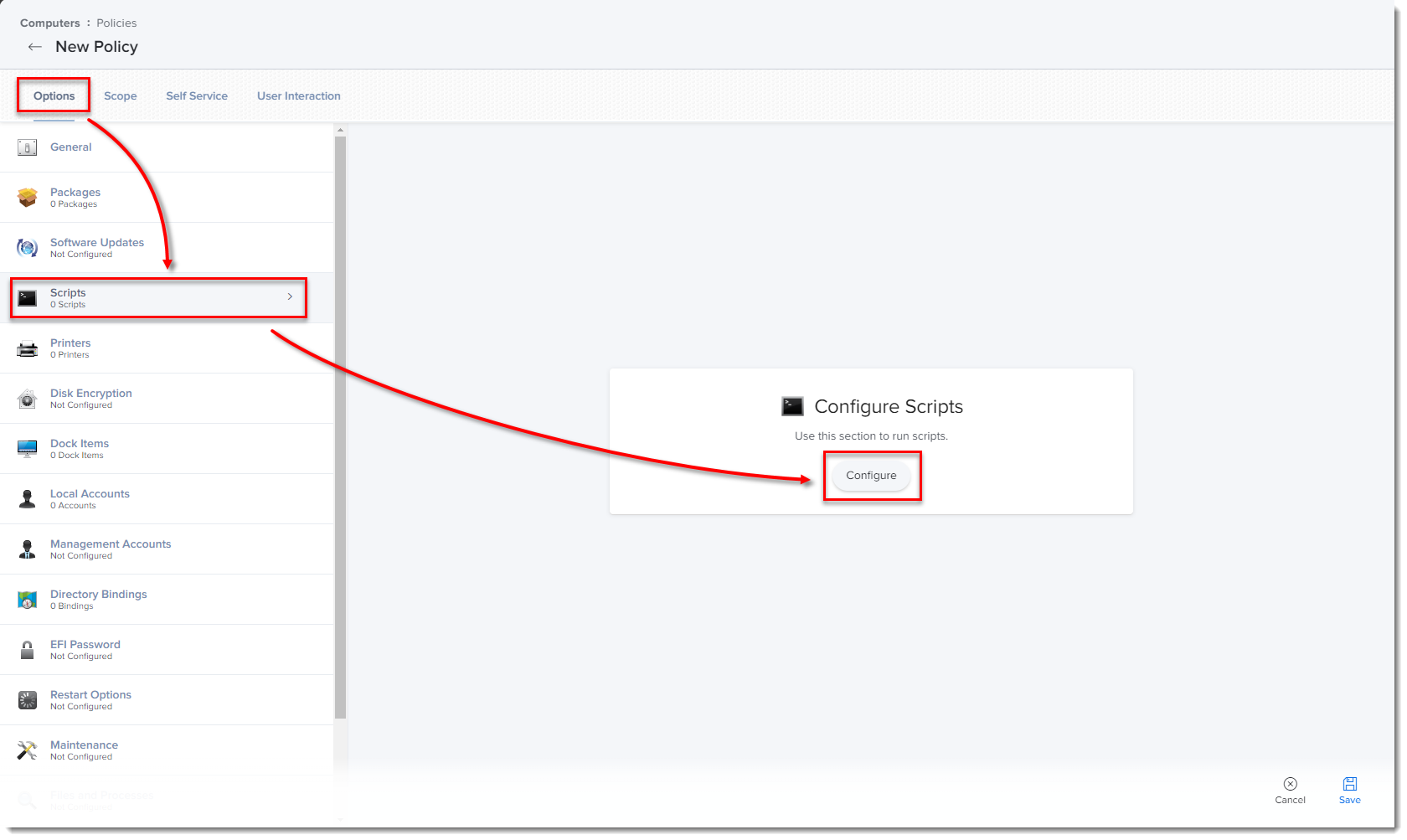
Figure 2-3
Click the image to view larger in new window -
Click Add to select the scripts to add to the policy.
-
Optionally, add the Parameter Values below for the Endpoint script.
-
Parameter 4 (Optional): Activate with EBA account information in the following format:
123-ABC-456:user=security.admin@mail.com:pass=SecurityAdminPass -
Parameter 5 (Optional): Specify HTTP Proxy in the format
http://Proxy-IP-or-FQDN:3128 -
Parameter 6 (Optional): If no parameter values is added, it will install the latest version of ESET Endpoint Security for macOS and need to be activated by the ESET PROTECT On-Prem server. If you want to install the latest version of ESET Endpoint Antivirus for macOS, type
EEA.
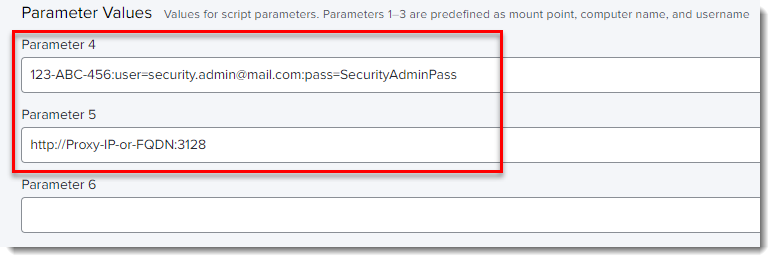
Figure 2-4 -
-
Click the Scope tab and click Add.
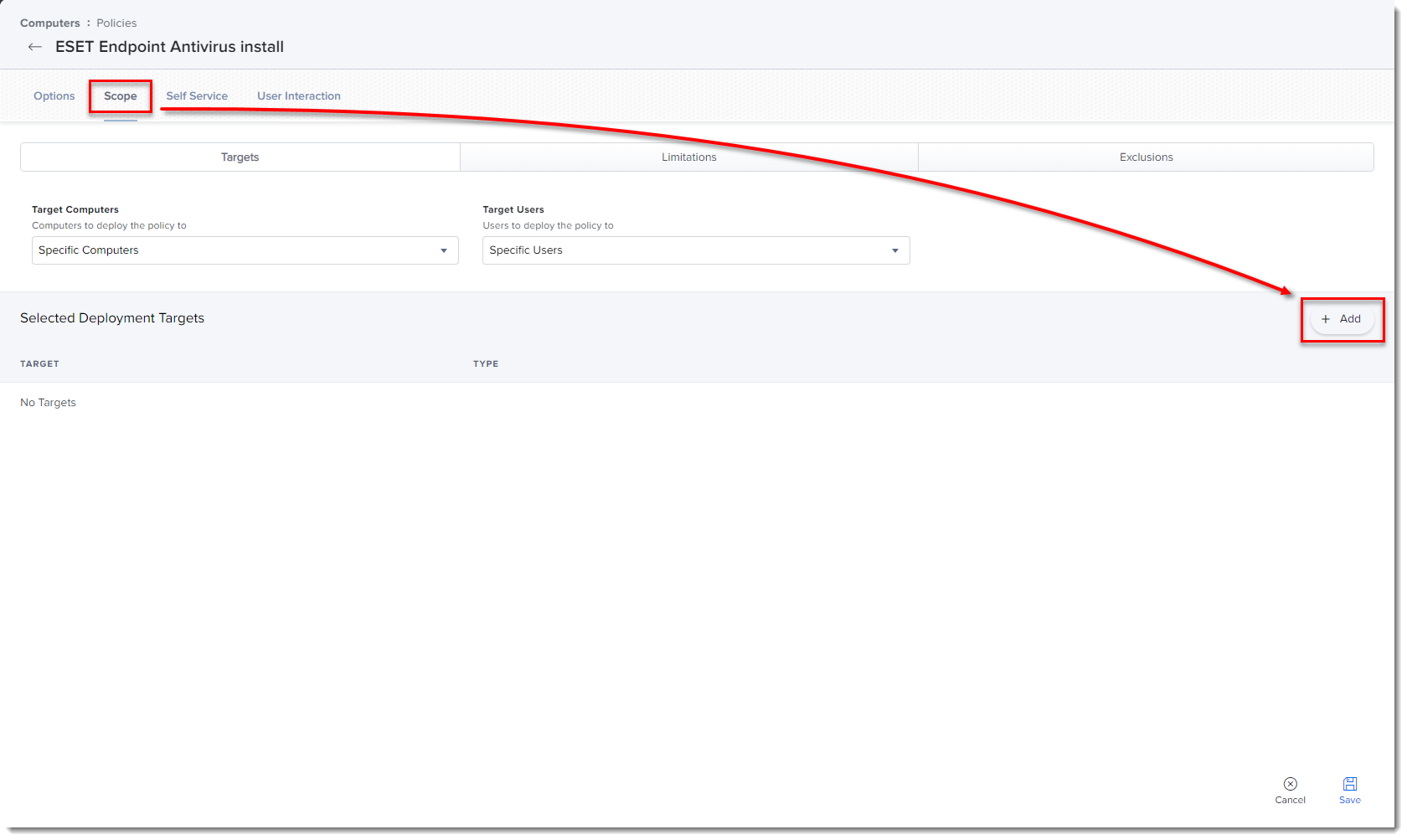
Figure 2-5
Click the image to view larger in new window -
In the Add Deployment Targets section, select the computers (or Computer Groups) you want to apply the policy to by clicking Add, and then click Done.
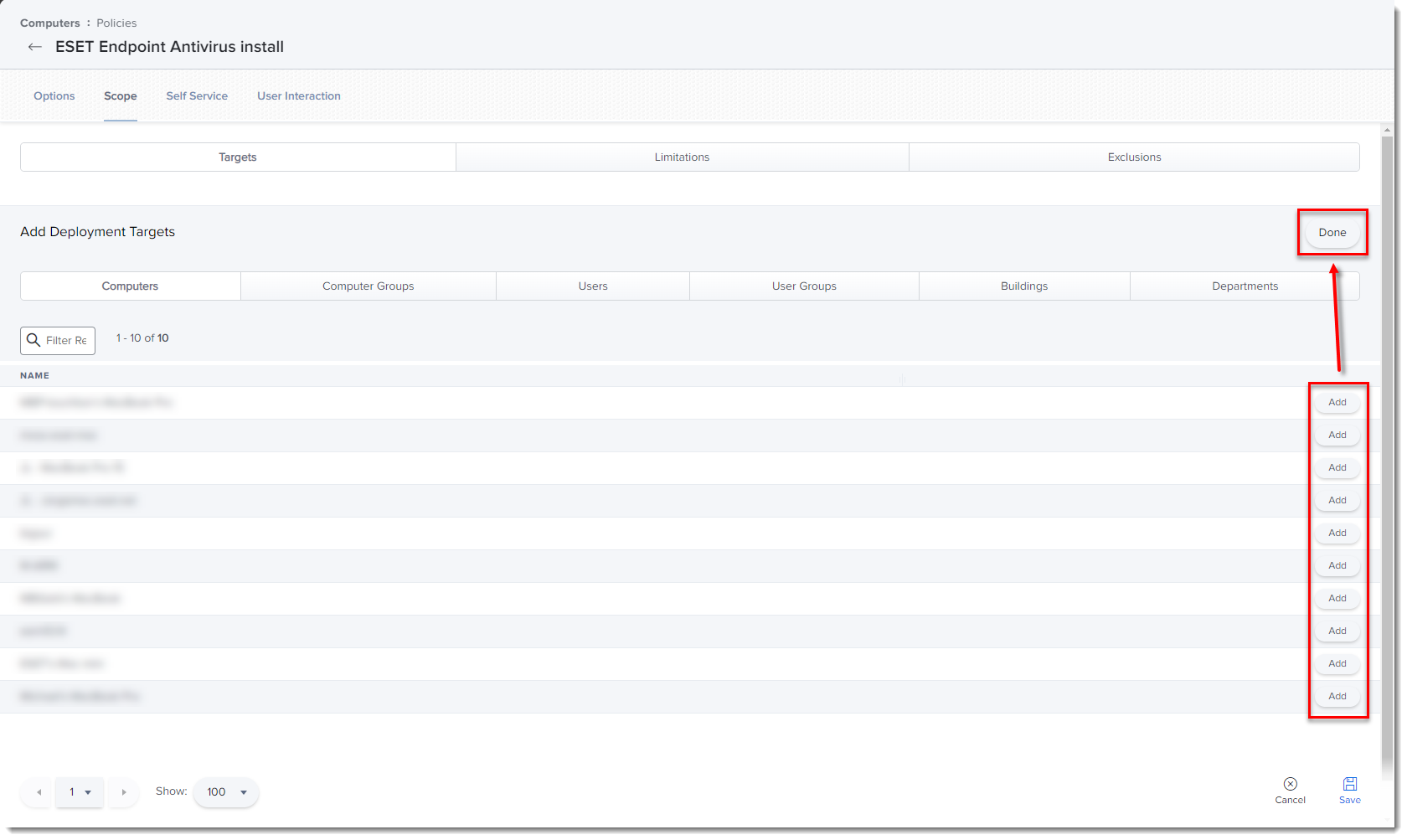
Figure 2-6
Click the image to view larger in new window -
Click Save to apply your changes.
III. Additional options
- Verify you can manage the ESET Endpoint using ESET PROTECT On-Prem: Open the ESET PROTECT Web Console, click Computers and verify that the Jamf endpoint is displayed in the All Group.
- If you did not type the License Key or Security Admin during the install scripts, you can activate the ESET products using ESET PROTECT.
- Extension Attributes: Extension Attributes show information regarding ESET products in the Computer details → Search Inventory → General section.
Follow the instructions below to add the Extension Attribute:
-
Open Jamf pro and click the All Settings gear icon → Computer Management → Extension attributes.
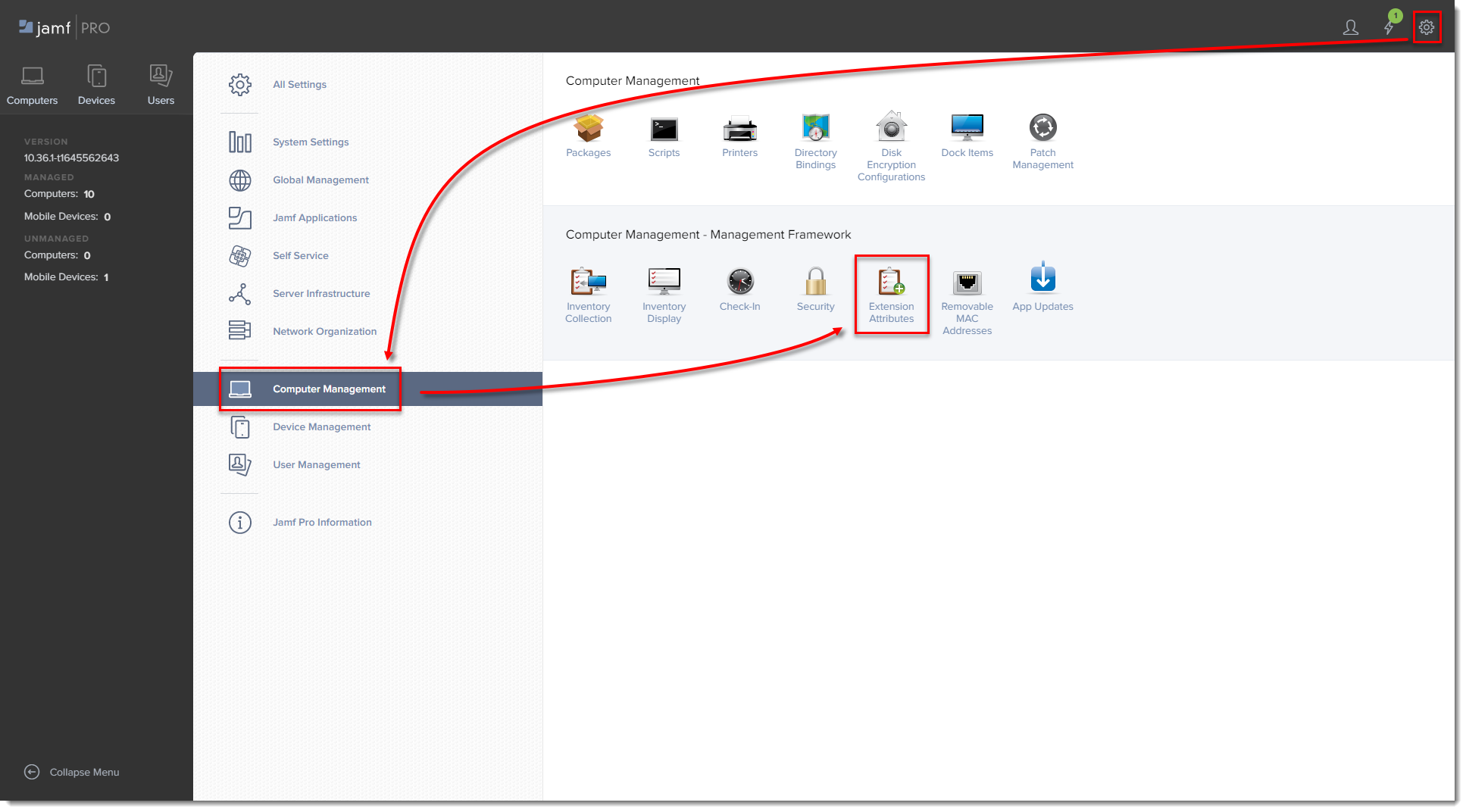
Figure 3-1
Click the image to view larger in new window -
Click New to create a new extension attribute.
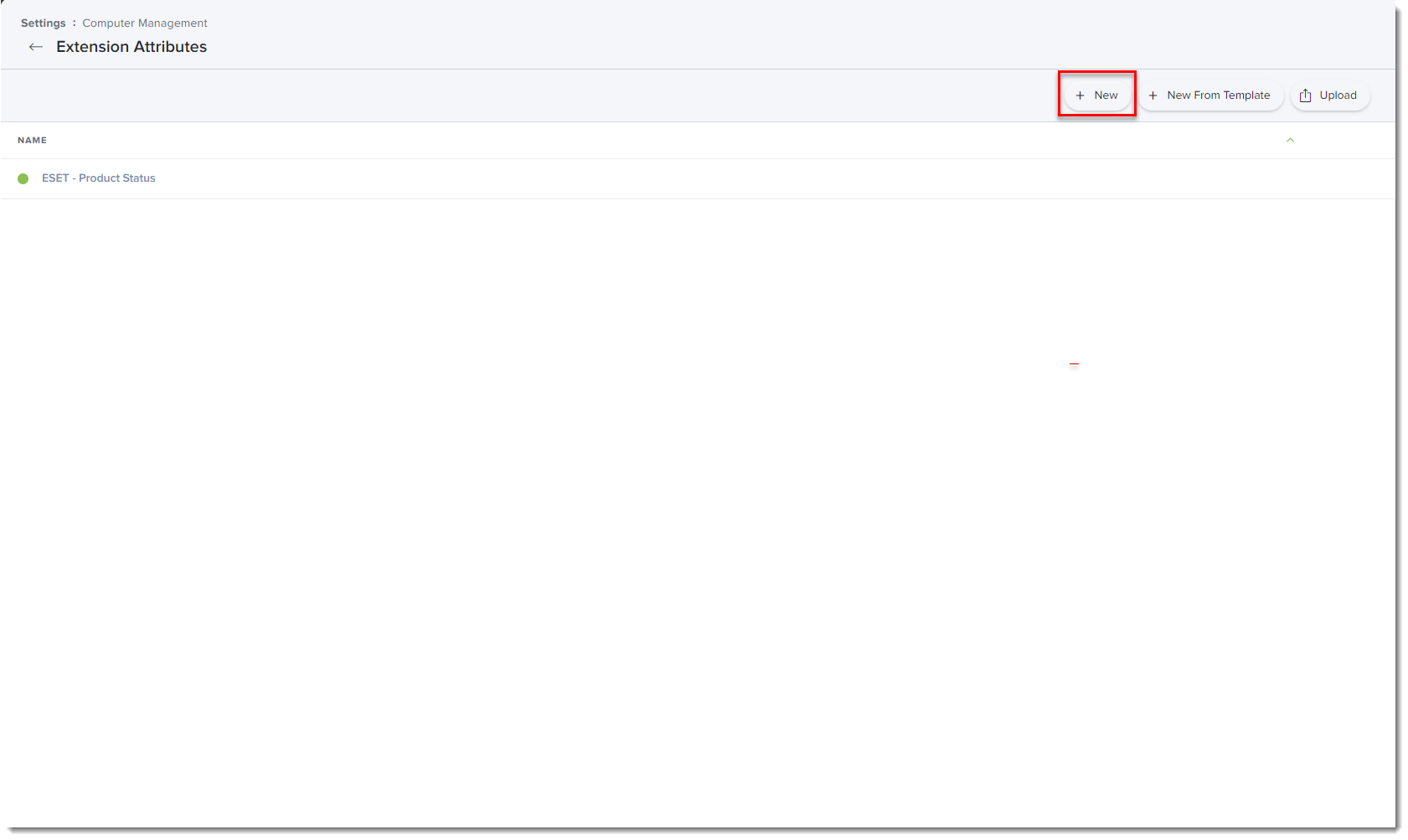
Figure 3-2
Click the image to view larger in new window -
In Display Name type a name for the extension attribute, select Script in the Input Type drop-down menu and then paste the ESETstatusEA.sh (right-click and select Save link as) script into the Shell field and click Save.
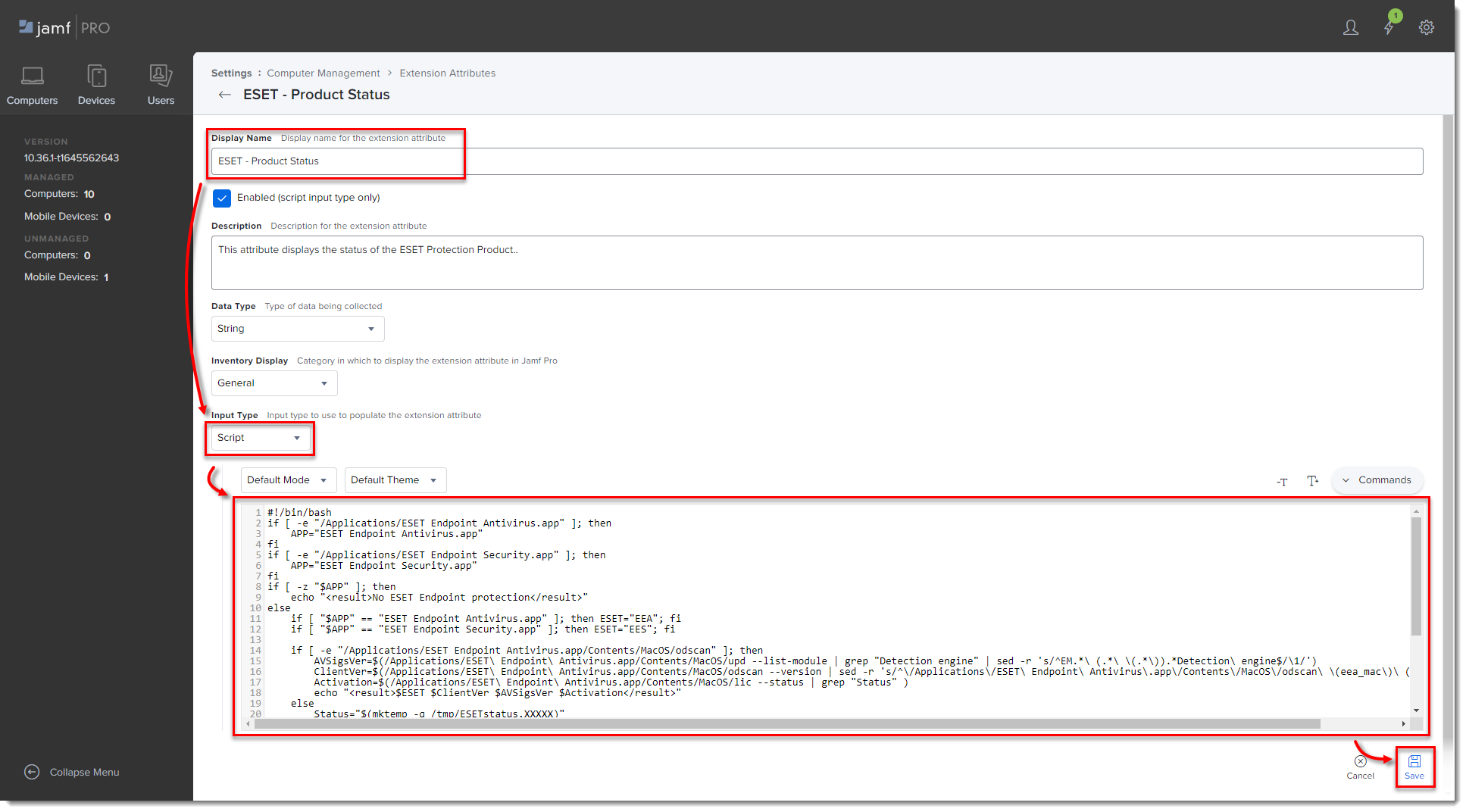
Figure 3-3
Click the image to view larger in new window -
The extension attribute will be automatically set to all computer groups. Click a computer and in the General section, it will display the extension attribute.
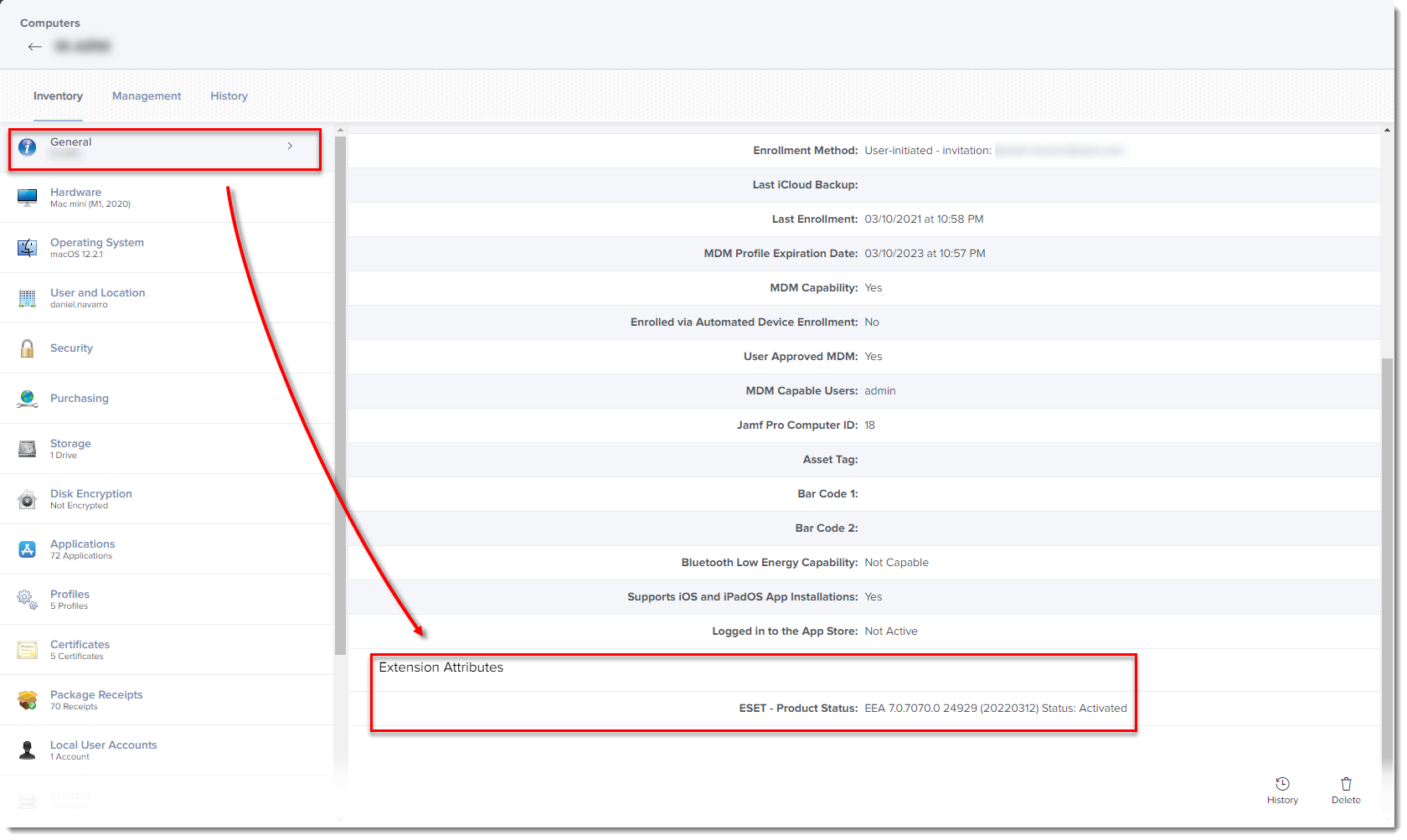
Figure 3-4
Click the image to view larger in new window
Troubleshooting issues after upgrading to version 8
Approve system extensions via MDM
In environments with a remote management tool such as JAMF or Kandji, the steps below will resolve the system extension issue. If you are currently using Endpoint for macOS version 7 without automatic updates enabled, follow these steps before upgrading to version 8 to avoid system extension conflicts.
-
Download the configuration profile .plist from the Endpoint Security User Guide.
-
Change the file extension from
.plisttomobileconfig. For exampleESET_enable_all.mobileconfig. -
In Jamf, navigate to computers → configuration profiles → select upload and select the file from step 2. In other management platforms, use the appropriate functionality to upload the configuration profile from step 2.
-
Assign the version 8 computers to the configuration profile scope and then click save. Extension alerts should begin to resolve within minutes.
-
Unassign the previously used configuration profiles(s) in JAMF or the management client. Only the version 8 configuration profile should be used with version 8.
ESET Endpoint Security for macOS Firewall is Automatically Enabled
With the upgrade to version 8, the firewall feature will be present and enabled upon installation.
To disable the firewall via an ESET PROTECT policy in environments where a firewall solution is already in place, follow these steps:
-
Navigate to Settings in the Common Features policy that is applied to macOS devices. In the Common Features policy, the macOS logo is missing but still applies.
-
Navigate to Settings → Network Access Protection → Firewall.
-
Click the toggle next to Enable Firewall to disable the setting.
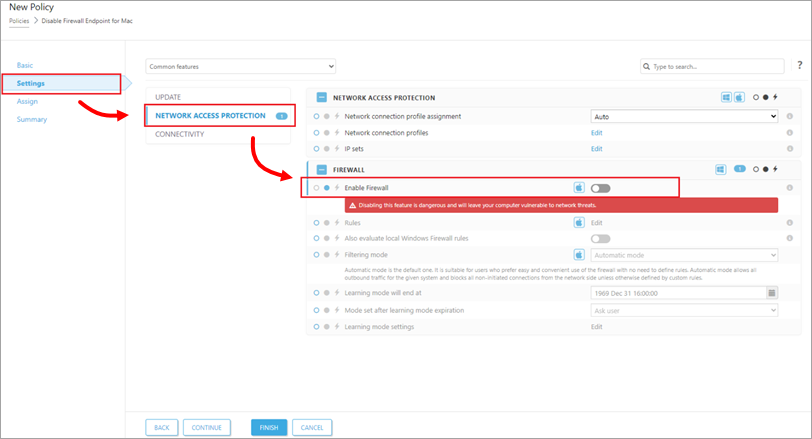
Figure 4-1