Issue
- Create a log of all connections blocked by the ESET firewall in ESET Endpoint Security
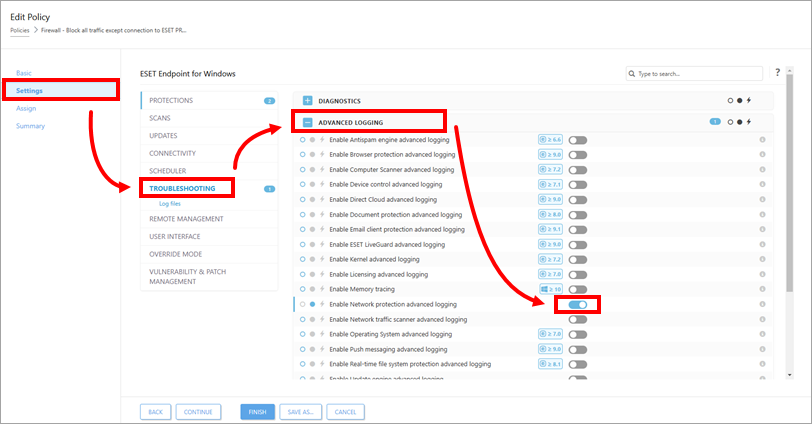
- Enable advanced logging of the Network protection in ESET Endpoint Security and ESET Endpoint Antivirus
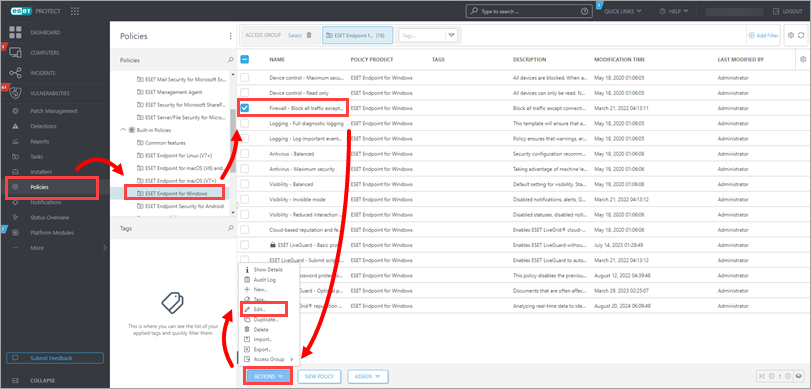
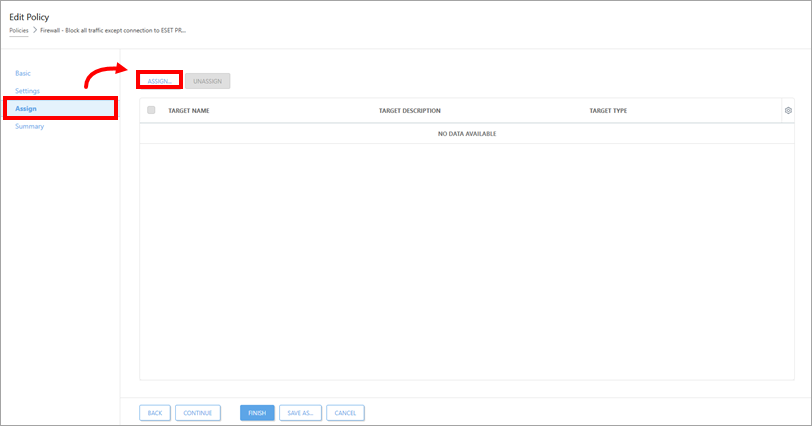
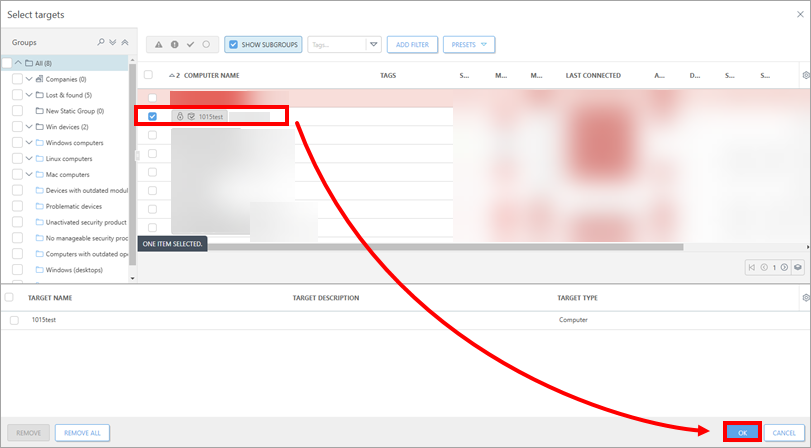
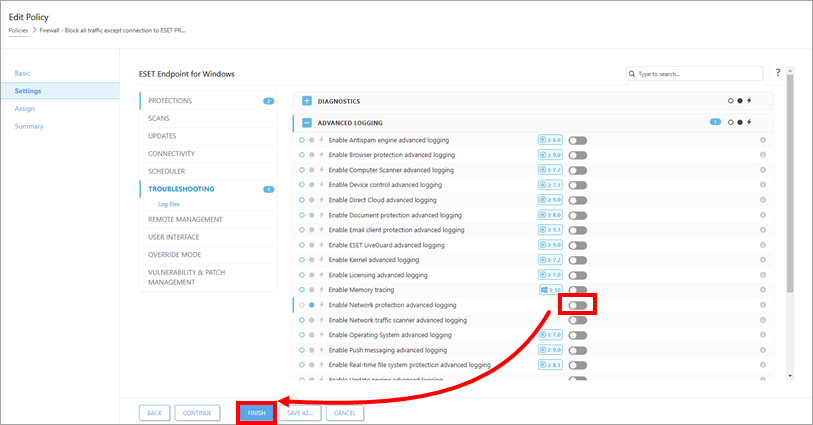
- I. Activate logging of blocked connections in ESET PROTECT or ESET PROTECT On-Prem
- II. Download and run the ESET Log Collector tool