Solution
Introduction
This article describes how to configure a Cyberoam® UTM appliance to authenticate users against an ESA Server. Cyberoam® SSL VPN, Captive Portal and IPsec VPN applications are supported. Before proceeding, verify that you've installed the RADIUS Server component of ESET Secure Authentication and can access the RADIUS service that allows external systems to authenticate users.
Before your Cyberoam® device can use the ESA Server to authenticate users via RADIUS, it must be set up as a RADIUS client on the ESA Server. Next, your server running the ESA RADIUS service must be setup as a RADIUS Server on the Cyberoam® device. Once these configurations have been specified, you can start logging into your Cyberoam® device using ESA OTPs.
Step I - RADIUS client configuration
To allow the Cyberoam® device to communicate with your ESA Server, you must configure the device as a RADIUS client on your ESA Server:
- Log in to ESA Web Console.
- Navigate to Components > RADIUS and locate the hostname of the server running the ESA RADIUS service.
- Click the hostname, then click Create New Radius Client.
- In the Basic Settings section:
- Give the RADIUS client a memorable name for easy reference.
- Configure the IP Address and Shared Secret for the Client so that they correspond to the configuration of your VPN appliance. The IP address is the internal IP address of your appliance. If your appliance communicates via IPv6, use that IP address along with the related scope ID (interface ID).
- The shared secret is the RADIUS shared secret for the external authenticator that you will configure on your appliance.
- In the Authentication section apply the settings shown in Figure 1-1 below.
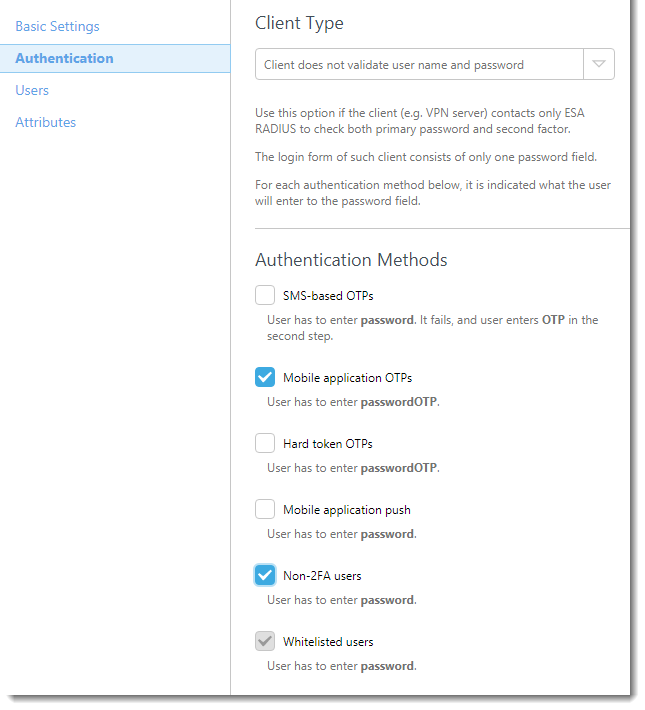
Figure 1-1
ESA has now been configured to communicate with the Cyberoam® device. You must now configure the Cyberoam® device to communicate with the ESA Server.
Step II - Configure the RADIUS server settings for your Cyberoam® device
Follow the steps below:
- Log in to the Cyberoam® Web Admin Console as an administrator.
- Navigate to Identity → Authentication → Authentication Server.
- Click Add (see Figure 2-1).
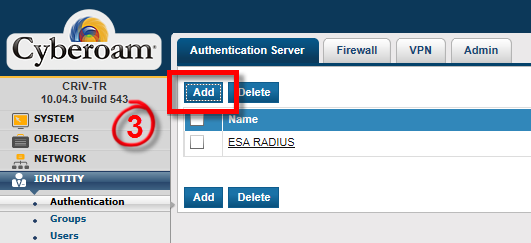
Figure 2-1
- Enter the following:
- Select RADIUS Server from the Server Type drop down.
- Server Name: A name for this server (for example, ESA-RADIUS).
- Server IP: The IP address of your ESA RADIUS Server.
- Authentication Port: 1812
- Shared Secret: Your RADIUS server shared secret (see Figure 1-1)
- Integration Type: Loose Integration
- Click Test Connection. Enter the credentials of your test user. Make sure that you are using a user with Mobile Application 2FA using ESA enabled. When prompted for a password, append the OTP generated by the ESA Mobile Application to your AD password. For example, if the user has an AD password of Esa123 and an OTP of 999111, you should type Esa123999111.
- Click on Test Connection. You should see a success status message in the bottom left, (see Figure 2-2). Do not proceed to Step III until the connectivity test is successful.
![]()
Figure 2-2
Step III - Enable ESA Authentication
- In the left panel, navigate to Identity → Authentication → VPN.
- Configure the relevant VPN Authentication Methods. For example, for SSL VPN Authentication, select "ESA RADIUS" as the authentication method, as per Figure 3-1.
- Click Apply, then OK.
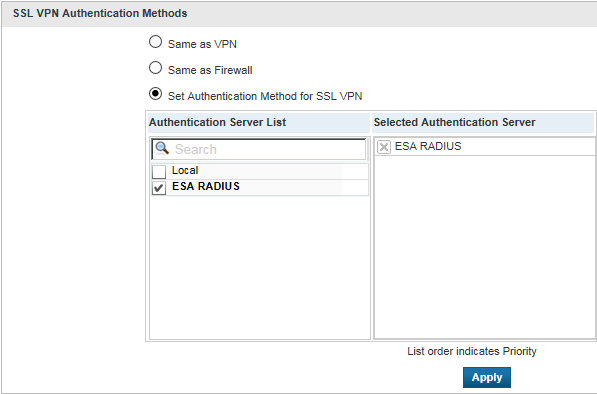
Figure 3-1
Step IV - Test the connection
To test the newly configured connection:
- Navigate to your sign-in page.
- Enter the following credentials using your test account:
- AD username in the Username field.
- AD password, concatenated with an OTP from their ESA Mobile application in the Password field.
Troubleshooting
If you are unable to authenticate via the ESA RADIUS server, make sure that you have performed the following steps:
- Run a smoke test against your RADIUS server, as per the Verifying ESA RADIUS Functionality.
- If no faults were fixed and you are still unable to connect, revert to an existing sign-in configuration that does not use 2FA and verify that you are able to connect.
- If you are able to connect using the old settings, restore the new settings and verify that there is no firewall blocking UDP 1812 between you VPN device and your RADIUS server.
- If you are still unable to connect, contact ESET technical support.