Issue
- Create a Dynamic Group Template
- Dynamic Group Template rule criteria list
- Examples of Dynamic Group templates
Solution
Create a Dynamic Group Template
-
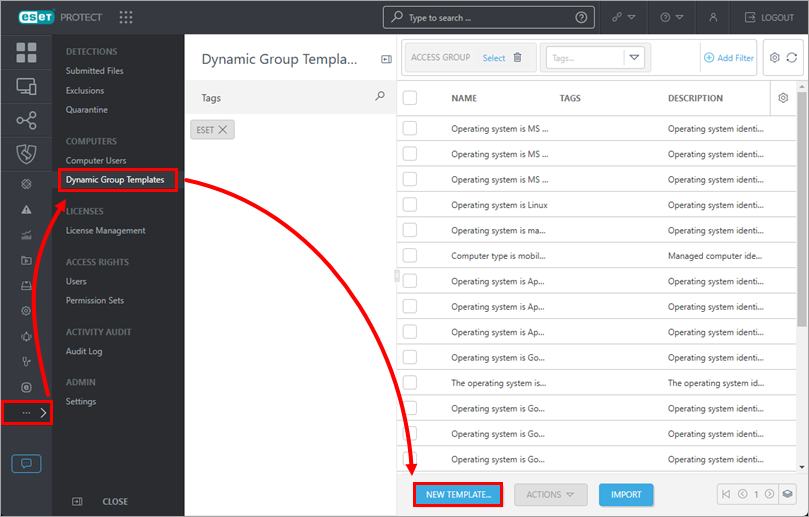
Click More → Dynamic Group Templates → New Template.
ESET PROTECT On-Prem users: Click More → Dynamic Group Templates → Add.
-
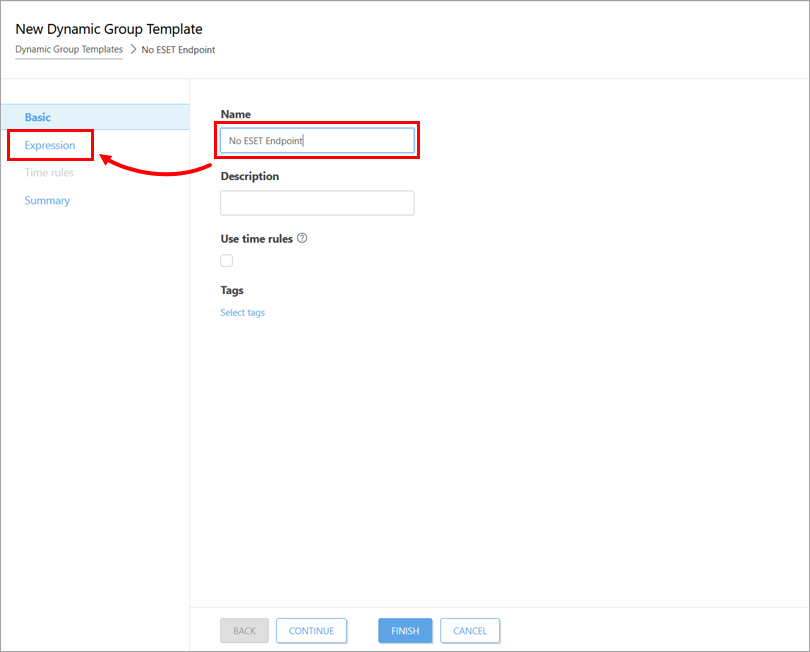
Type a name for the new Dynamic Group Template into the Name field and click Expression.
-
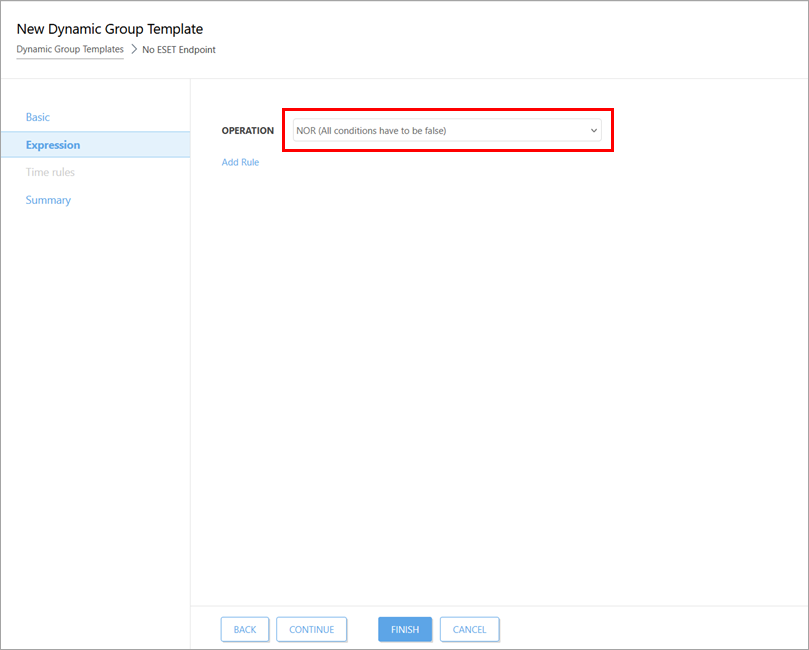
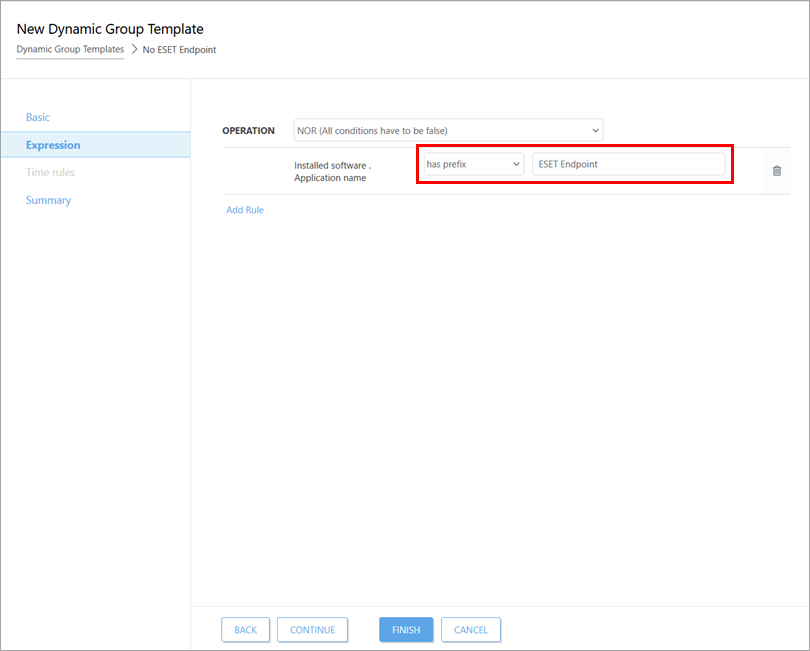
Select an operation from the Operation drop-down menu. This operation will be performed for all rules you add.
In this example, select NOR (All conditions have to be false).
-
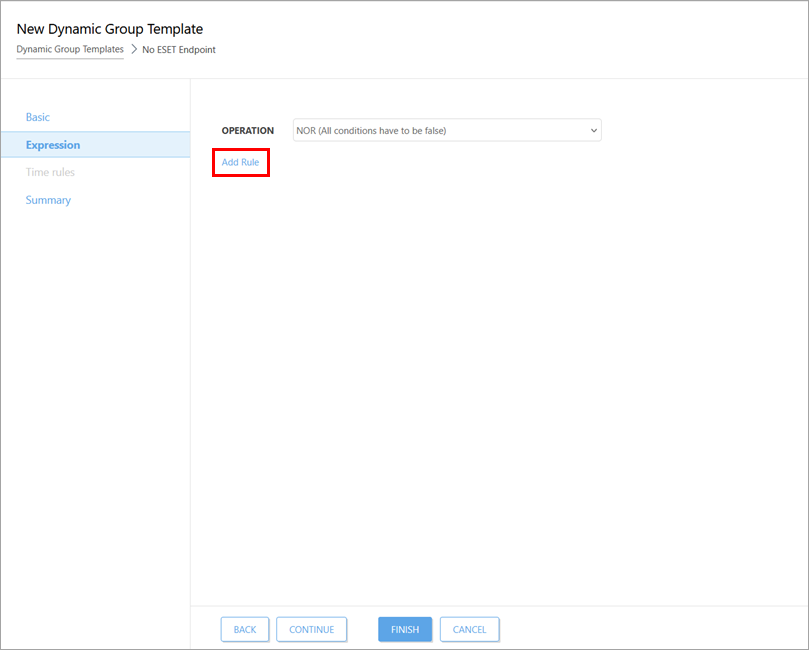
Click Add Rule. A rule consists of a criterion, a logical connector, and a value.
-
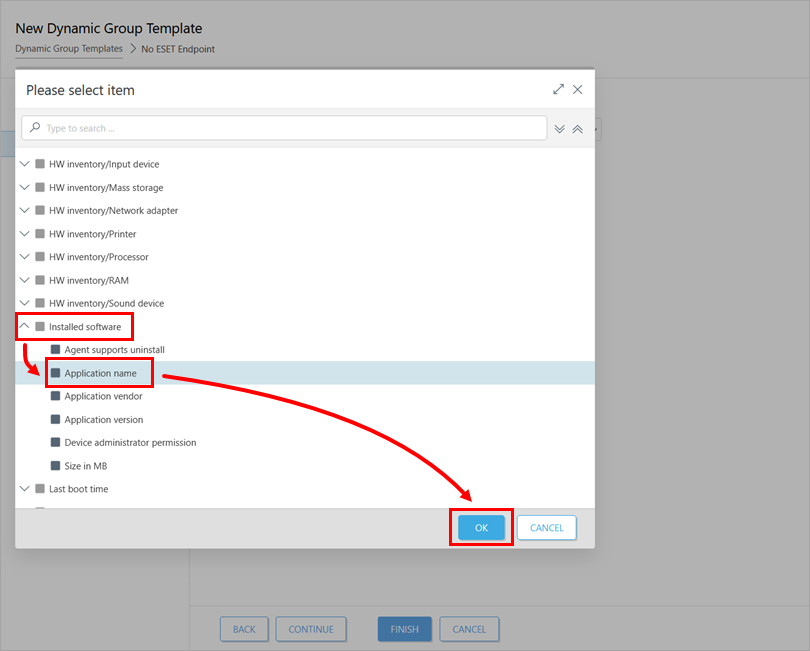
Select a rule criterion. See the Dynamic Group Template rule criteria list for more information about the available criteria.
In this example, click Installed software → Application name → OK.
-
Select a logical connector for the rule criteria and specify a value for the rule criteria. See Dynamic Group Template logical connectors for more information about available logical connectors.
In this example, select has prefix from the logical connector drop-down menu and type ESET Endpoint into the value field.
-
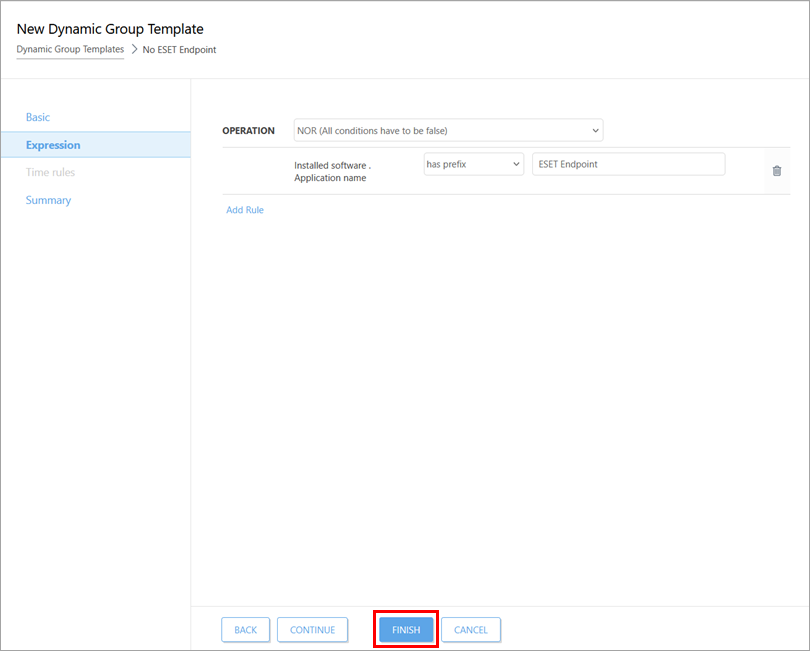
Click Finish. If this is a new template, create a dynamic group using the new template.
In this example, you have created a Dynamic Group Template that will add all devices without installed software that have a name prefix ESET Endpoint to the specified dynamic group.
Dynamic Group Template rule criteria list
Click the expander below to see all available criteria for rules in the Dynamic Group Template expression configuration.
Criteria list
Activation
- Activated by ESET PROTECT—Group devices based on whether they were activated or are not activated by ESET PROTECT or ESET PROTECT On-Prem
- Location ID
- Module code
- Seat name
- Subscription code
- Subscription flags
- Subscription model status
- Subscription model type
- Subscription module code
- Subscription module name—Group devices based on the subscription name
- Subscription renewal period
- Subscription type
- Subscription validity
Active detections
- Detection engine—Group devices based on which Detection engine version they are currently using or whether their Detection engine was released before or after a specific date
- Detection handled
- Detection name
- Detection type
- First seen time
- Hash of detected file
- Object URI—Group devices based on the Uniform Resource Indicator associated with a found threat
- Process name—Group devices based on part or all of the process names associated with a found threat
- Restart required—Group devices based on whether they require a restart
- Scan log reference—Group devices based on whether a specific item is referenced in their scan log
- User—Group devices based on the user currently logged in
Computer
- Computer—Group all devices except for a specific computer together, or select a single computer to treat as a group
- Managed applications mask—Group devices based on whether they are or are not covered by one of the pre-defined managed application masks
Device identifiers
- Identifier type—Group devices based on the type of identifier they use, FQDN, Computer Name, Computer Workgroup, IMEI or Serial Number
- Identifier value—Group devices based on part or all of a specific identifier value
Functionality/Protection problems
- Feature—Group devices based on which product features require attention
- Problem—Group devices based on the error notification ESET is displaying. Select from a list of available error notifications
- Source—Group devices based on the ESET PROTECT component, client solution, or operating system identified as the source of an issue
- Status—Group devices based on their indicated status. Select from Malfunction, OK, Security Notification, and Security risk
- Trace
Functionality/Protection status
- Source—Group devices based on the ESET PROTECT component, client solution, or operating system identified as the source of an issue
- Status—Group devices based on their indicated status. Select from Malfunction, OK, Security Notification, and Security risk
Functionality/Protection status of computer
- Status—Group devices based on their indicated status. Select from Malfunction, OK, Security Notification, and Security risk
Hardware
- Running on battery—Group devices based on whether they are discharging (running on battery power), not discharging (running using a power adapter), or not present.
HW inventory/Chassis
- Description
- Identifier
- Manufacturer—Group devices based on the manufacturer
- Serial number
- Type
HW inventory/Cloud
- Cloud provider
- Location
- Machine type
- Name
- Resource identifier
HW inventory/Device information
- Device manufacturer
- Device model
- Firmware type
- Firmware version
- Serial number
- Trusted Platform Module (TPM) Version
HW inventory/Display
- Description
- Identifier
- Manufacturer
- Serial number
HW inventory/Display adapter
- Architecture type
- Description
- Identifier
- Manufacturer
- Memory size [MB]
- Memory type
- Refresh rate (max) [Hz]
HW inventory/Input device
- Description
- Identifier
- Manufacturer
- Type
HW inventory/Mass storage
- Description
- Hardware Encryption Status
- Identifier
- Manufacturer
- Serial number
- Storage capacity [MB]
- Type
HW inventory/Network adapter
- Connection name
- Description
- MAC address
- Manufacturer
- Type
HW inventory/Printer
- Description
- Identifier
- Location type
- Marking type
- Printing type
- Resolution (horizontal - vertical) [pixels per inch]
HW inventory/Processor
- Architecture type
- Clock speed [MHz]
- Description
- Identifier
- Manufacturer
- Number of cores
- Number of logical cores
HW inventory/RAM
- Architecture type
- Capacity [MB]
- Clock speed [Hz]
- Description
- Identifier
- Manufacturer
- Serial number
HW inventory/Sound device
- Description
- Identifier
- Manufacturer
Installed software
- Agent supports uninstall—Group computers with agent versions that support the agent uninstall task
- Application name—Group devices that have a specific application installed or not installed
- Application vendor—Group devices with software from a specific vendor installed
- Application version—Group devices with a specific version of an application
- Device administrator permission—Group devices based on whether you have administrator permissions on them or not
- Size in MB—Group devices based on the amount of drive space in MB that is used by software
Last boot time
- Last boot time
Logged users
- Domain—Group devices based on whether they log in to a specific domain
- Full name—Group devices based on the full name of the device's user
- Username—Group devices based on the name of the user currently logged in
- Origin
Mobile network
- Cellular technology—Group devices based on the cellular network they use
- eSIM
- Home subscriber MCC—Group devices based on their Mobile Country Code (MCC)
- Home subscriber MNC—Group devices based on their Mobile Network Code (MNC)
- Phone number—Group devices based on their phone number
- Roaming subscriber—Group devices based on whether or not they are roaming
- Roaming subscriber MCC—Group devices based on their roaming Mobile Country Code
- Roaming subscriber MNC—Group devices based on their roaming Mobile Network Code
- SIM carrier network—Group devices based on their SIM carrier network
- SIM unique serial number—Group devices based on their SIM unique serial number or a range of SIM serial numbers
- Subscription ID
Network adapters
- Adapter name—Group devices based on the name of the network adapter installed
- MAC address—Group devices based on their MAC address
- Order—Group devices based on whether they are using their primary or secondary network adapter
Network DNS servers
- IP DNS server—Group devices based on their use of a specific DNS server IP address or an address within a specified range
- Order—Group devices based on whether they are using their primary or secondary DNS server
Network gateways
- IP gateway—Group devices based on the IP address of the network gateway they use
Network IP addresses
- Adapter IP address—Group devices based on their network adapter IP address
- Adapter subnet mask—Group devices based on the subnet mask they use
- Address type—Group devices based on whether they use an IPv4 or IPv6 address
- IP subnetwork—Group devices based on their IP subnetwork
- MAC address—Group devices based on their MAC address
- Order—Group devices based on whether they are using their primary or secondary network IP address
Network WINS servers
- IP WINS server—Group devices based on the IP address of the WINS server they use
- Order—Group devices based on whether they are using their primary or secondary WINS server
OS edition
- OS build number
- OS name—Group devices based on the name of the operating system they use
- OS platform—Group devices based on the platform of the operating system they use
- OS security patch
- OS service pack—Group devices based on whether they use a specific service pack or a range of service packs
- OS type—Group devices based on the type of operating system they use
- OS version—Group devices based on the version of the operating system they use
OS locale
- OS language—Group devices based on the language of the OS they use
- OS locale—Group devices based on the locale of the OS they use
Peer certificate
- Issuer
- Product
- Serial number
- Status
- Subject
- Valid from
- Valid till
Patch management
- Application name
- Application vendor
- Application version
- Patch version
Performance
- Idle state—Group devices based on whether they are or are not in an idle state
Quarantine
- Detection name
- Excludable—Group devices based on whether items in the quarantine can be excluded from scanning
- Hash—Group devices based on the hash of items in the quarantine
- Hits—Group devices based on whether they have a specific number of quarantined items or have more or less than that number of items
- Object name—Group devices based on whether an object with a specific name is quarantined
- Restorable—Group devices based on whether items in the quarantine can be restored to their original locations
- Size—Group devices based on whether items in the quarantine can be restored to their original locations
- Time of first occurrence—Group devices based on the time that a given threat was first quarantined
- Time of last occurrence—Group devices based on the time that a given item was last quarantined
Spam top domains
- Count—Group devices based on whether they have received a certain number of spam emails from a given domain
- Domain—Group devices that log in to domains associated with the highest number of spam messages
Spam top recipients
- Count—Group devices based on whether they have received a certain number of spam emails
- Recipient—Group devices that receive the highest amount of spam email
Spam top senders
- Count—Group devices that have sent a certain number of spam emails
- Sender—Group devices that send the highest number of spam emails
Storage devices
- Storage capacity [MB]—Group devices based on storage capacity in MB
- Storage encryption status—Group devices based on whether they use encrypted or unencrypted storage
- Storage ID—Group devices based on the ID of their primary storage device
- Storage type—Group devices based on the presence of a specific type of storage. Select Compact disc, Local disk, Network drive, Removable disk, or unknown drive type
Storage devices capacity
- Free space [%]—Group devices based on the amount of free space available in percent
- Free space [MB]—Group devices based on the amount of free drive space available in MB
- Storage ID—Group devices based on the ID of their primary storage device
Time zone
- Time zone—Group devices based on the time zone they use
- Time zone offset [minutes]—Group devices based on the time zone offset they use in minutes
- Application name
- Application vendor
- Application version
- Category
- CVE
- Patch uuid
- Score

