Issue
ESET products detect and block XData malware as a Win32/Filecoder.NLN and AES-NI as Win32/Filecoder.AESNI.
- Your ESET product detected a Win32/Filecoder.AESNI infection
- Decrypt your files using the ESETAESNIDecryptor.exe tool
- Your personal files have become encrypted
- Your files have been renamed with one of the following extensions: .aes256, .lock, .aes_ni_0day, .aes_ni, .decrypr_helper@freemail_hu, .~xdata~
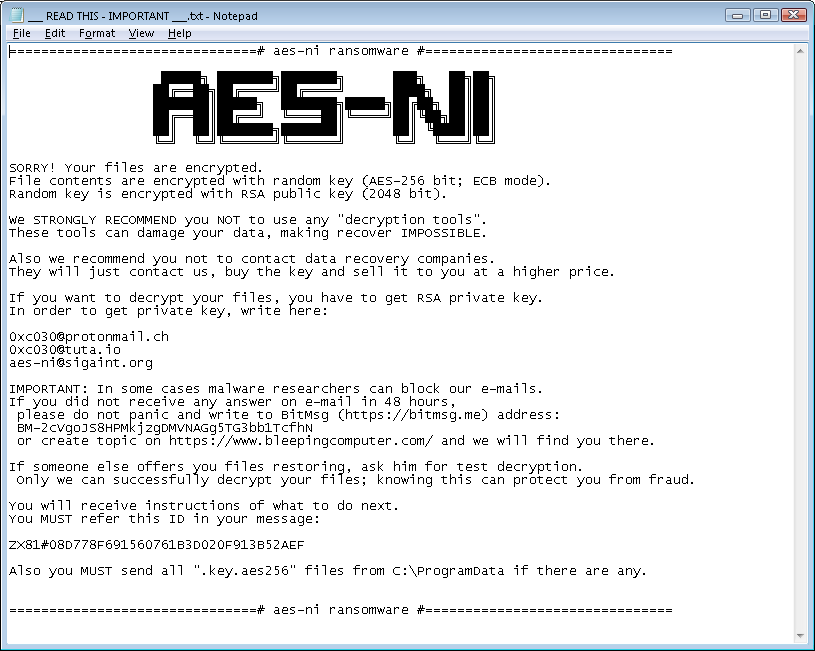
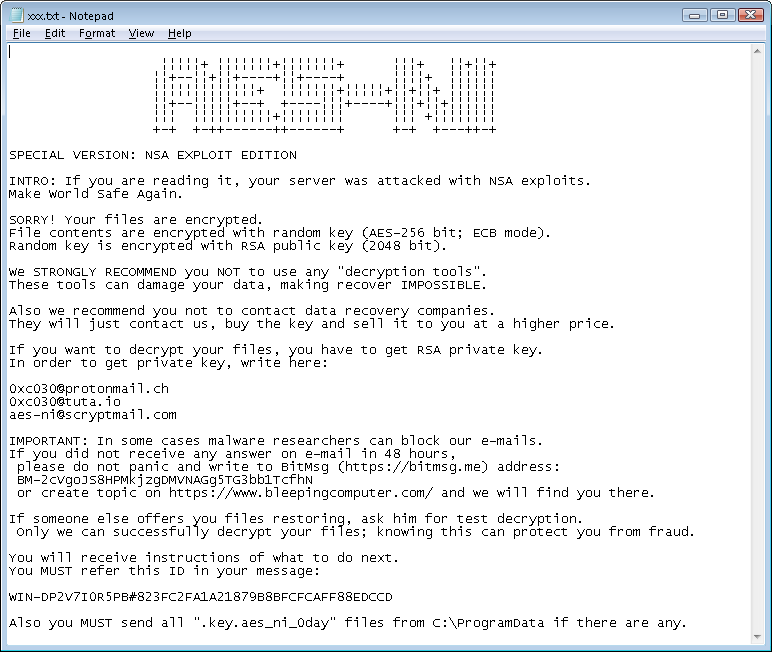
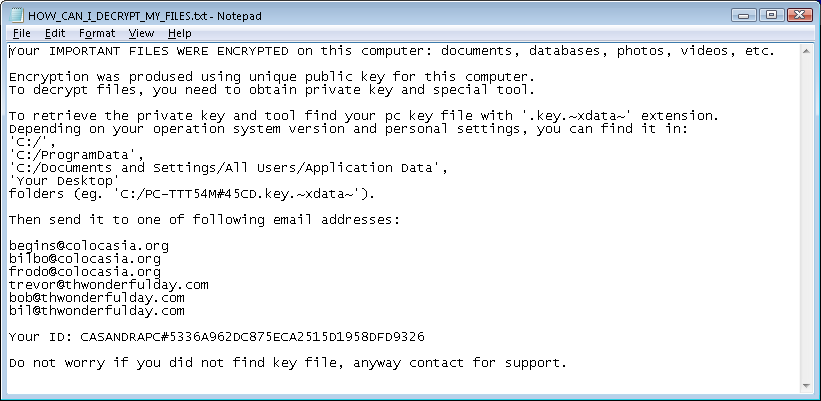
- You receive one of the following notes on your computer's desktop background, or in a .txt, .html or .png file:
- "YOUR FILES ARE ENCRYPTED!"
- "If you want to decrypt your files, you have to get RSA private key."
- "all your data was crypted to get it back write to aes-ni@prontomail.com"
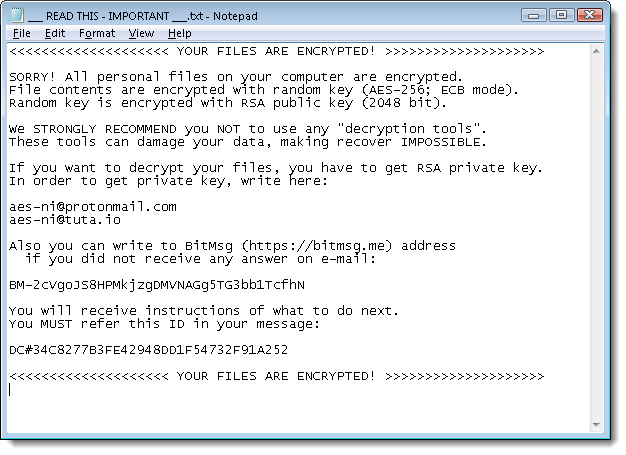
Figure 1-1
Click +Details for more information and additional images associated with this ransomware
Details
Win32/Filecoder.AESNI is a trojan that encrypts files on local drives. The user is told they must send information and make a payment using the Bitcoin payment service in order to decrypt their files.
- XData ransomware making rounds amid global WannaCryptor scare
- ESET releases decryptor for AESNI ransomware variants, including XData
- Win32/Filecoder.AESNI threat description on virusradar.com
Examples of AES-NI key file names
- USER-43FF24E2A8#7988C10CEA4CBE5453802CE852506660-decrypr_helper NEW-2017421111129-542.key
- PC#7F8FF538043FDBDFAD07DBF085DE9910-SPECIAL NEW-201753011433-276.key.aes_ni
- PC#7F8FF538043FDBDFAD07DBF085DE9910-Bravo NEW-2017530113345-902.key.aes_ni_0day
- PC#7F8FF538043FDBDFAD07DBF085DE9910-#-201753182943-932.key.~xdata~
Image gallery
Solution
- Download the ESET AES-NI decryptor tool and save the file to your desktop.
ESETAESNIDecryptor.exe
- Click Start → All Programs → Accessories, right-click Command prompt and then select Run as administrator from the context menu.
- Windows 8 / 8.1 / 10 users: press the Windows key + Q to search for applications, type Command prompt into the Search field, right-click Command prompt and then select Run as administrator from the context menu.
- Windows 8 / 8.1 / 10 users: press the Windows key + Q to search for applications, type Command prompt into the Search field, right-click Command prompt and then select Run as administrator from the context menu.
- Type the command
cd %userprofile%\Desktop(do not replace "userprofile" with your username–type the command exactly as shown) and then press Enter.
- Type the command
ESETAESNIDecryptor.exeand press Enter.
- Read and agree to the end-user license agreement.
- Type
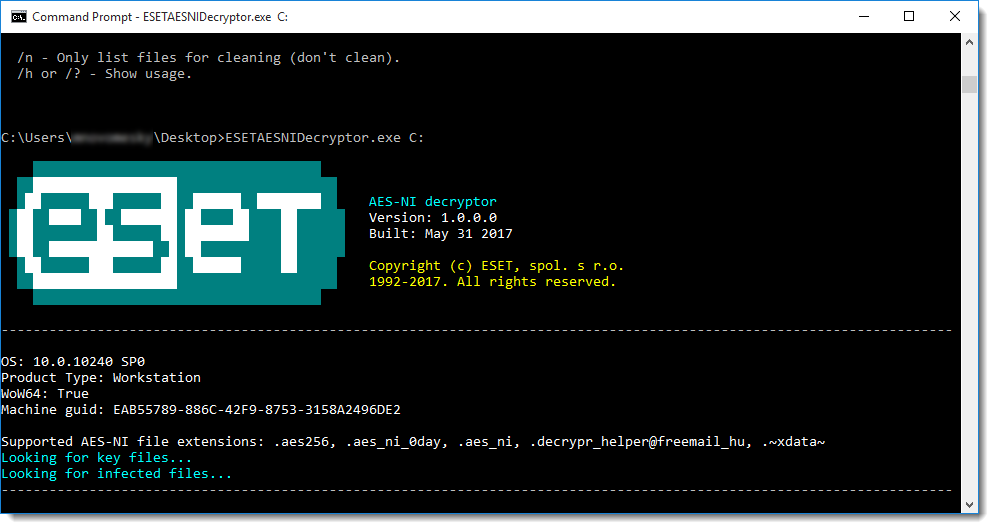
ESETAESNIDecryptor.exeC:and press Enter to scan the C drive. To scan a different drive replaceC:with the applicable drive letter.
- The ESET AES-NI decryptor tool will run and the “Looking for key files...” message will be displayed. After that "Looking for infected files..." message will be displayed. If an infection is discovered, follow the prompts from the ESET AES-NI decryptor tool to clean your system.
Figure 1-2