Issue
- Cannot configure the ESET Remote Administrator appliance to join a domain
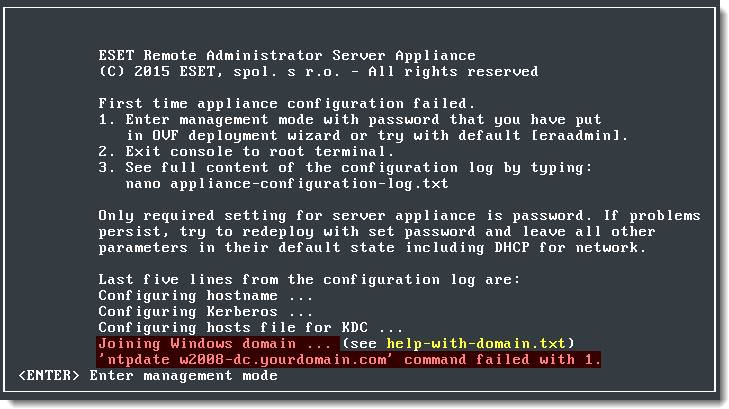
Figure 1-1
Solution
This issue is most likely the result of an incorrectly configured ovf.xml file.
To resolve this issue, open the appliance-configuration-log.txt file to examine the exact error message. To do so on your Virtual appliance, follow the steps below:
- Enter management mode by pressing the Enter key on your keyboard.
- You will be prompted for your password. Type the password you specified during deployment and press Enter.
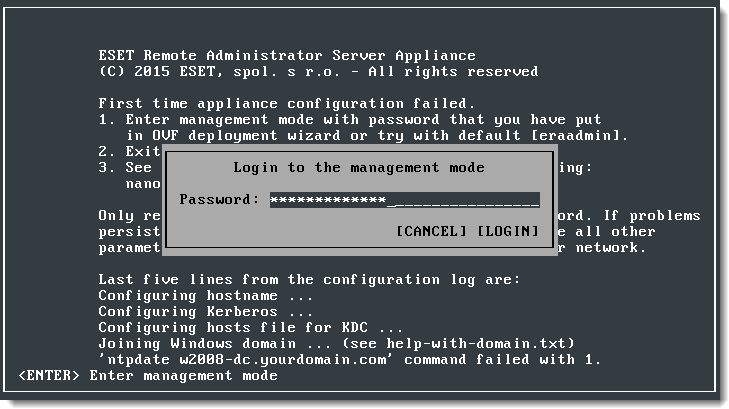
Figure 1-2
- Choose Exit console using the arrow keys and press Enter.
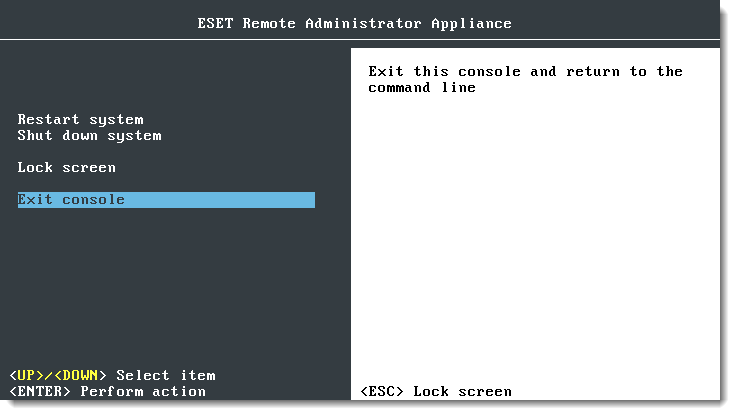
Figure 1-3
- Type nano appliance-configuration-log.txt as root in the terminal and press Enter to open appliance-configuration-log.txt in Nano Editor. Look for error messages to find out what could be causing the issue.
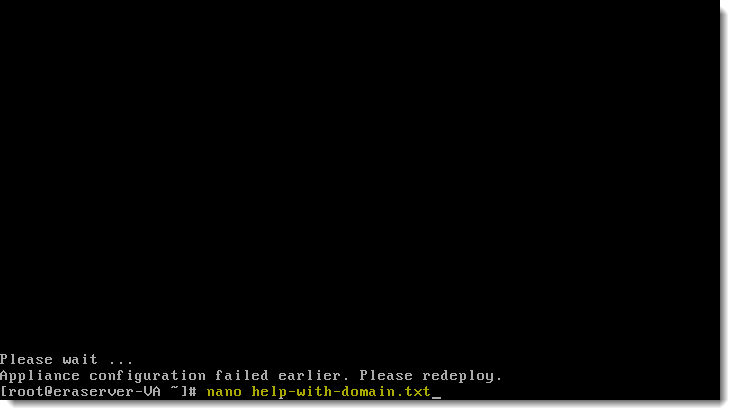
Figure 1-4
Follow the steps below to troubleshoot the issue:
A. Verify that the parameters you put into the appliance during configuration of the ovf.xml file are correct. For example, if you are joining the domain 'yourdomain.com', configuration parameters for ERA Server Virtual appliance would be:
- Hostname: "eraserver.yourdomain.com". It is important that hostname is FQDN.
- Windows Domain: "yourdomain.com". It is important to have at least one '.' character as delimiter in the domain name. Automation script will take first token ('yourdomain' in this case) and fill it as workgroup into the /etc/samba/smb.conf as uppercase text.
- Windows Domain Controller: 'Win2008DC.yourdomain.yourdomain.com". FQDN of a domain controller—not an ip address.
- Windows Domain Administrator: "Administrator". With this login and password below one should be able to login in to the domain controller without problem and do administrator changes.
- Windows Domain Administrator Password: "xxxxx". Password for Administrator account.
- DNS: IP address of the domain controller. This should be set if default DNS server is not able to resolve hostnames for the specified domain above. This parameter will tie the appliance with DNS server in the domain controller.
If you are sure that all parameters are correct, check whether the configuration generated by the automation script is correct.
B. Check the following configuration files:
- Hosts file:
/etc/hostsshould correctly map domain controller name and its IP address. - Kerberos configuration:
/etc/krb5.confshould be correctly generated. Check that 'kinit' works. - Crontab configuration:
/etc/crontabshould contain record for regular time updates against domain controller. - Samba configuration:
/etc/samba/smb.confshould be correctly generated.
If all configuration files are correct, then proceed with manual domain join.
C.Join the domain manually:
- Call '
net ads join -U Administrator%' to join the domain. If successful, you should see created computer record in domain controller. - Start '
service winbind start'. - Start '
service nmb start'. - Start '
service smb start'. - Verify that you can ping Winbind using'
wbinfo -p'. - Verify that '
wbinfo -u' lists domain users and 'wbinfo -g' lists domain groups.
ERA Server uses the commands 'kinit' and 'ldapsearch' to browse through active directory and 'wbinfo' and 'ntlm_auth' to perform domain authentication. If these commands work, then you have successfully joined your domain.