詳細
ESET Secure Authentication を使用して、公開 Web リソースまたは VPN 接続用の第 2 要素を Microsoft® TMG Server に追加できます。
ソリューション
はじめに
この記事では、Microsoft® Forefront Threat Management Gateway サーバーを構成して、ESA サーバーに対してユーザーを認証する方法について説明します。先に進む前に、ESET Secure Authentication の RADIUS Server コンポーネントがインストールされており、外部システムがユーザを認証するための RADIUS サービスにアクセスできることを確認してください。
TMG サーバが ESA サーバを使用して RADIUS 経由でユーザを認証する前に、ESA サーバ上で RADIUS クライアントとしてセットアップする必要があります。次に、ESA RADIUSサービスを実行しているサーバーを、TMGサーバー上のRADIUSサーバーとしてセットアップする必要があります。 これらの設定が指定されると、ESA OTPを使用してTMG VPNまたはWebリソースへのログインを開始できます。
ステップI - RADIUSクライアントの設定
RADIUSプロトコルでは、RADIUSサーバーへのアクセス要求にRADIUSクライアント(例えば、Microsoft® TMG Sever)のIPアドレスを含める必要があります。
Microsoft® TMG Server が ESA Server と通信できるようにするには、ESA RADIUS Server 上で TMG Server を RADIUS クライアントとして設定する必要があります:
- ESA Web Console にログインします。
- Components > RADIUS]に移動し、ESA RADIUSサービスを実行しているサーバのホスト名を探します。
- ホスト名をクリックし、[新しいRadiusクライアントを作成]をクリックします。
- 基本設定]セクションで
- RADIUSクライアントに覚えやすい名前を付けます。
- クライアントのIPアドレスと 共有シークレットをVPNアプライアンスの設定に対応するように設定します。IP アドレスは、アプライアンスの内部 IP アドレスです。アプライアンスが IPv6 経由で通信する場合は、関連するスコープ ID(インターフェース ID)と共にその IP アドレスを使用します。
- 共有シークレットは、アプライアンスで構成する外部認証機能の RADIUS 共有シークレットです。
- 認証セクションで、以下の図 1-1 に示す設定を適用します。
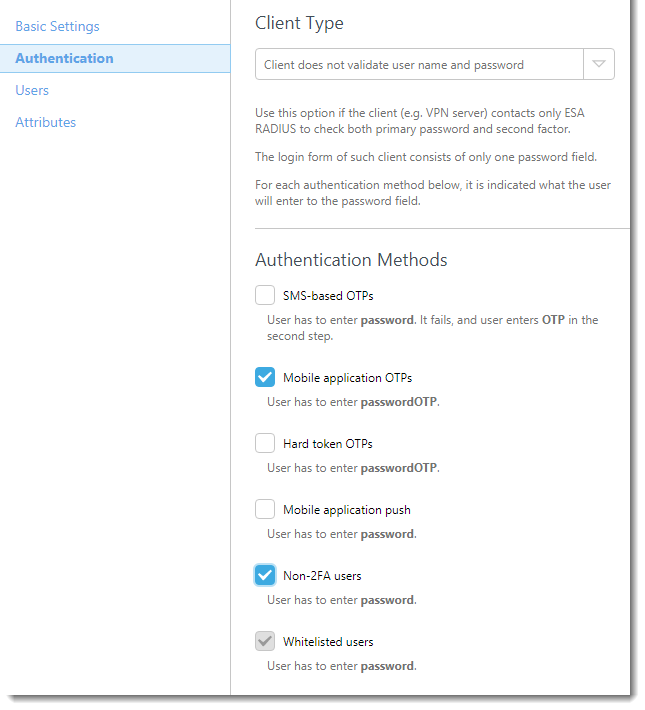
図 1-1
これで ESA は Microsoft® Forefront TMG サーバと通信するように構成されました。ここで、Microsoft® TMG Server Web Listener を構成して ESA Server と通信するか、Microsoft® TMG Server VPN Client Access を構成して ESA Server と通信する必要があります。
Webリスナーを構成する手順については、以下のステップIIを参照してください。
VPNクライアント・アクセスの構成手順については、以下のステップIIIを参照してください。
ステップII - ウェブ・リスナーの構成
Webリスナーを構成するには、以下の手順に従います:
- Forefront TMG Managerを起動します。
- Forefront TMGを展開し、 ファイアウォールポリシーに移動します。
- 関連するファイアウォールルール(この Web リスナーに関連付けられているルール)を右クリックし、コンテキストメニューから[Properties]を選択します。
- リスナー]タブに移動し、ドロップダウン メニューからこの Web リスナーを選択して[プロパティ]をクリックします。
- 認証]タブに移動し、[クライアント認証方法]セクションのドロップダウンから[HTML フォーム認証]を 選択します。
- 認証検証方法]セクションで[RADIUS]ラジオボタンを選択し、[検証サーバーを構成する...]をクリックします。
- Add(追加)]をクリックして、ESA RADIUSサーバを以下のように設定します:
サーバ名: ESA RADIUSサーバのホスト名またはIPアドレス。
Server description(サーバーの説明): サーバーのフレンドリーな名前
共有秘密:ステップIで構成した共有秘密
認証ポート: 1812
タイムアウト: 30秒 - OK を クリックし、再度OK をクリックして変更を保存します。
- 適用 」をクリックして、サーバー構成を更新する(図 2-1 を参照)。
図 2-1
ログインに使用する URL に移動し、テスト用の資格情報を入力して、リストナーが構成されていることを確認します:
- ESA を使用して Mobile Application 2FA を有効にしたユーザを使用していることを確認する。
- パスワード・フィールドに、モバイル・アプリケーションによって生成された OTP を AD パスワードに追加する。たとえば、ユーザーのADパスワードが「ABCD」でOTPが「111999」の場合、「ABCD111999」と入力します。
ステップIII - VPNクライアントアクセスの設定
VPNクライアントアクセスを設定するには、以下の手順に従ってください:
- Forefront TMG Managerを起動します。
- Forefront TMGを展開し、[ リモートアクセスポリシー(VPN)]に移動します。
- 一番右のペインで[認証方法の選択]をクリックします。
- 認証]タブに移動します。図 3-1 に従って、PAP または MS-CHAPv2 のいずれかを選択します。
- 図 3-2 に示すように、「RADIUS」タブに移動し、「Use RADIUS for authentication」チェック・ボックスが有効になっていることを確認する。
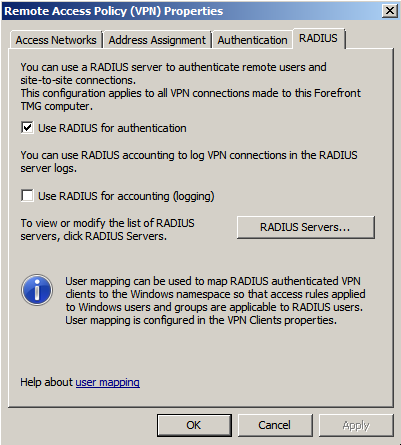
図 3-1
- RADIUS Servers...」をクリックし、以前に構成したESA RADIUSサーバを選択するか、「Add...」をクリックして、以下のようにESA RADIUSサーバを構成します:
Server name(サーバ名): ESA RADIUSサーバのホスト名またはIPアドレス。
Server description(サーバの説明): サーバのフレンドリーな名前
共有秘密:ステップIで構成した共有秘密
認証ポート: 1812
タイムアウト: 30秒 - OKをクリックし、もう一度OKを クリックする。
すべての変更が保存されたら、もう一度「Apply 」をクリックしてサーバーの構成を更新する(図 3-3 を参照)。
図3-2
TMGへの接続に通常使用するVPNクライアントを起動して、セットアップをテストする。テスト・ユーザーの認証情報を入力する:
- ESA を使用してモバイル・アプリケーション 2FA を有効にしたユーザを使用していることを確認する。
- パスワード・フィールドに、モバイル・アプリケーションが生成したOTPをADパスワードに追加します。たとえば、ユーザーのADパスワードが「ABCD」でOTPが「111999」の場合、「ABCD111999」と入力します。
トラブルシューティング
ESA RADIUSサーバで認証できない場合は、次の手順を実行してください:
- ESA RADIUS 機能の検証」に従って、RADIUS サーバに対してスモーク・テストを実行します。
- 障害が修正されず、まだ接続できない場合は、(2FAを使用しない)既存のサインイン構成に戻して、接続できることを確認する。
- 古い設定を使用しても接続できる場合は、新しい設定を復元し、VPNデバイスとRADIUSサーバー間のUDP 1812をブロックしているファイアウォールがないことを確認します。
- それでも接続できない場合は、ESETのテクニカルサポートにお問い合わせください。