Solution
Required user permissions
This article assumes that you have the appropriate access rights and permissions to perform the tasks below.
If you use the default Administrator user or are unable to perform the tasks below (the option is unavailable), create a second administrator user with all access rights.
- ESET PROTECT users: Create a second administrator user in ESET PROTECT
- ESET PROTECT On-Prem users: Create a second administrator user in ESET PROTECT On-Prem
![]() Endpoint users: Perform these steps on individual client workstations.
Endpoint users: Perform these steps on individual client workstations.
Create IDS exclusions in ESET PROTECT or ESET PROTECT On-Prem
-
Open ESET PROTECT or ESET PROTECT On-Prem in your web browser and log in.
-
Click Policies → ESET Endpoint for Windows, click the three dots next to the policy you want to edit and then click Edit.
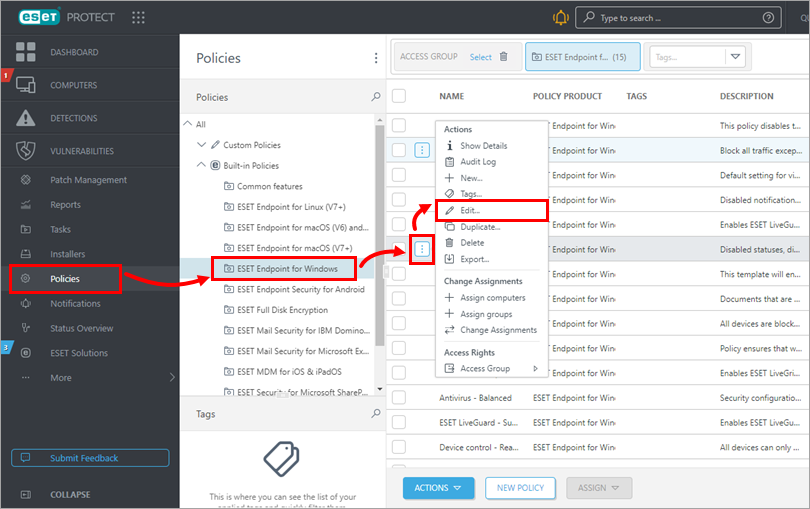
Figure 1-1
-
Click Settings → Protections → Network access protection → Network Attack Protection and click Edit next to IDS rules.
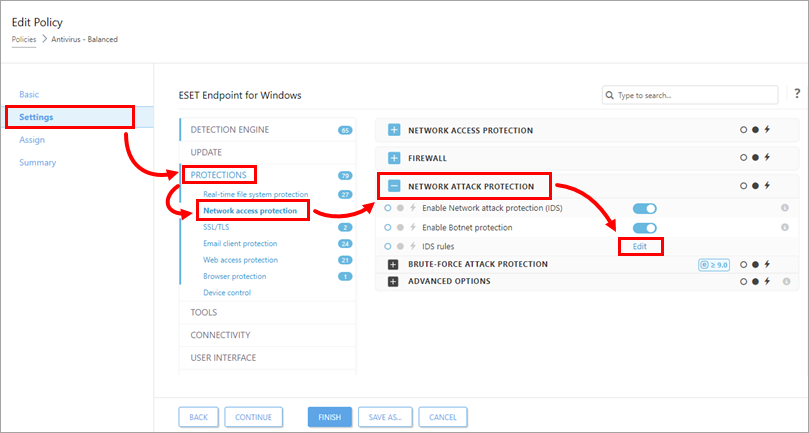
Figure 1-2
-
Click Add.
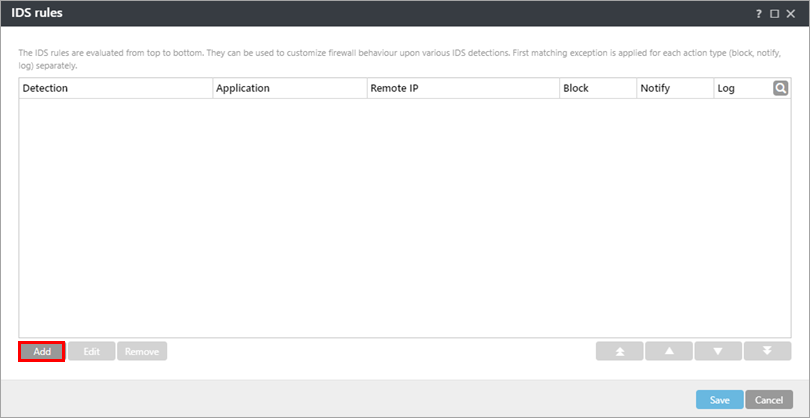
Figure 1-3 -
In the Detection drop-down menu, select Any Detection and type the Remote IP address (IP address of the machine with the software that scans the network).
Alternatively, you can set up an IDS exclusion for a locally installed app by typing the full path to the
.exefile in Application, for example,C:\Windows\system32\cmd.exe.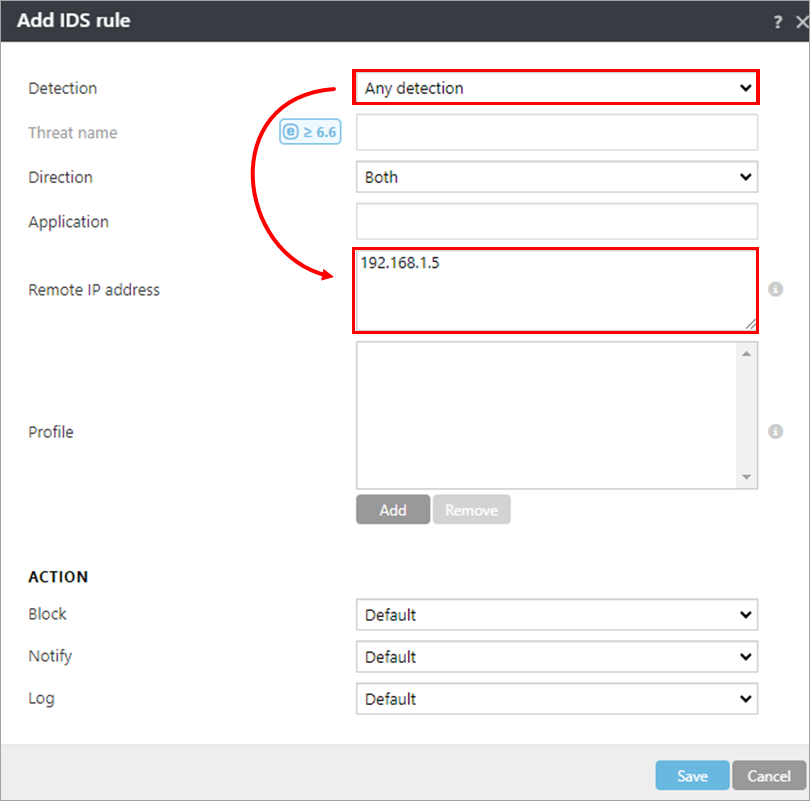
Figure 1-4 -
In the Action section, select No from each drop-down menu. Click Save → Save to save the policy. If this is a new policy, assign it to the correct groups. After the computers check-in, they will receive the policy change.
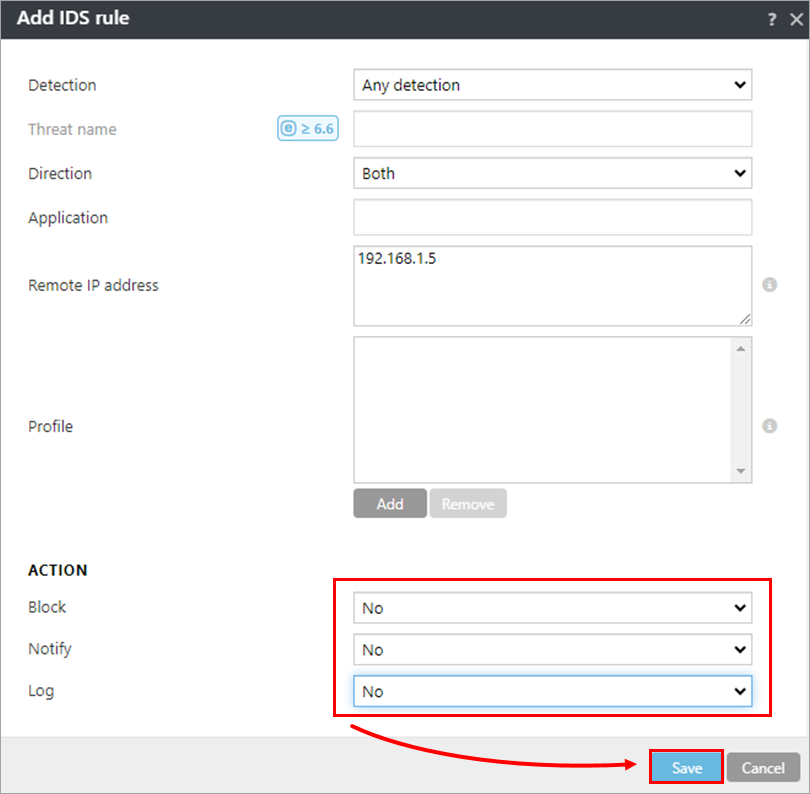
Figure 1-5