Issue
- "ICMP attack" or "DNS Cache poisoning attack" is detected by the ESET firewall
- "Detected ARP cache poisoning attack" is detected by the ESET firewall
- ESET Technical Support directed you to this article to flush your DNS cache and restore the Microsoft Hosts file
- Create an exception for internal IP traffic
- Run the DNS Flush tool (DNS poisoning only)
Details
Solution
If the ESET firewall detects a threat to your system, create an exception for internal IP traffic. Run the DNS flush tool if the issue is not resolved.
Create an exception for internal IP traffic
-
Determine if the IP address detected in the notification is a number that falls within the following range (where "x" is 0-255):
- 172.16.x.x–172.31.x.x
- 192.168.x.x
- 10.x.x.x
-
Review the IP addresses in the notification:
- If the IP address detected is within the safe range listed above, open the main program window of your ESET Windows product and skip to step 3.
- If the IP address detected is not within the safe range listed above, or there are no network peripherals currently in use on your network, the device detected by the firewall is located on a public network and could be a threat to your system. See the ESET DNS-Flush tool section and use it to repair any files that may have been damaged by DNS cache poisoning.
-
Click Protections, click Network access protection and click Edit next to IP sets.
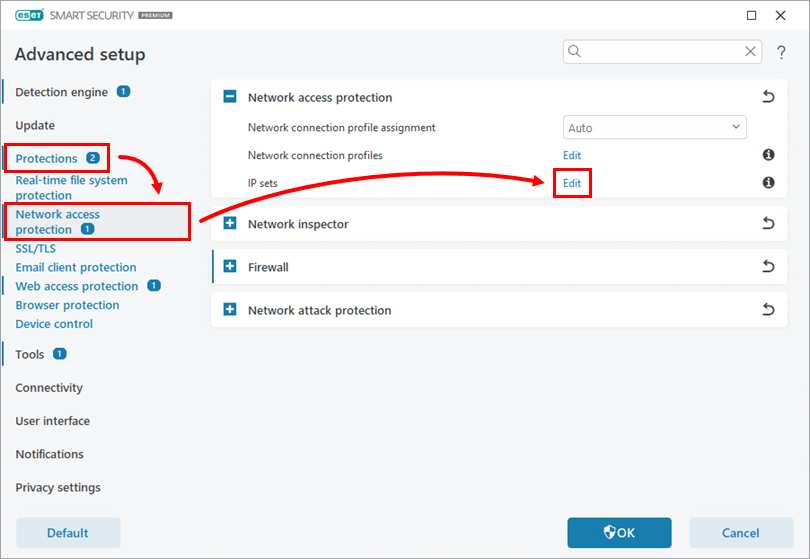
Figure 1-1 -
In the IP sets window, select Addresses excluded from IDS and click Edit.
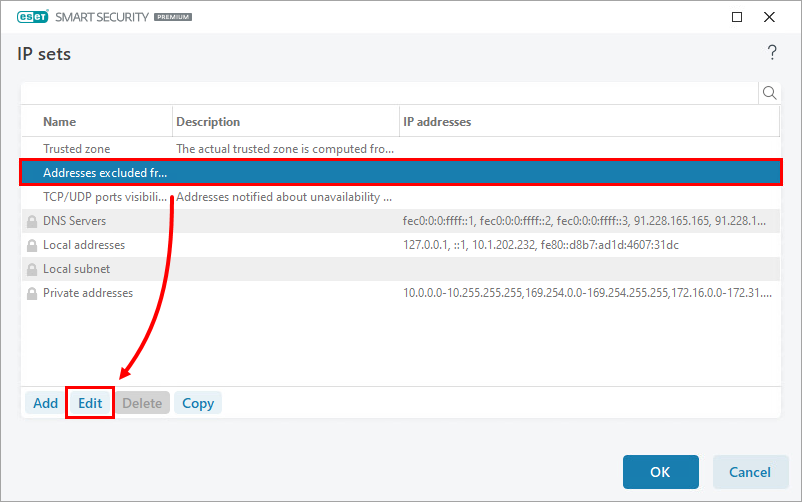
Figure 1-2 -
Type the device's IP address being incorrectly detected as a threat in the Remote computer address (IPv4, IPv6, range, mask) field. Click OK three times to save your changes and to exit Advanced setup.
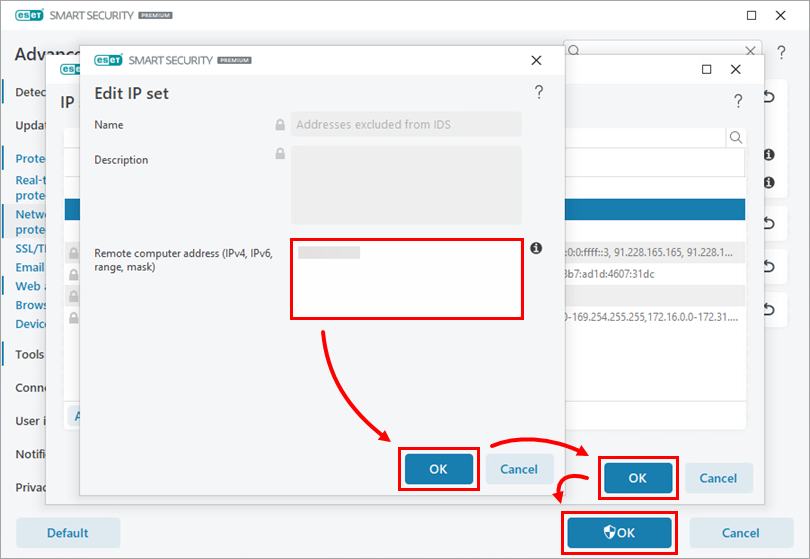
Figure 1-3
You should no longer see any messages about attacks from an internal IP address that you know to be safe. If you continue to experience this issue, proceed to solution 2 below.
Run the DNS Flush tool (DNS poisoning only)
Instead of entering ipconfig /flushdns to Command Prompt, you can use the ESET DNS Flush tool to flush your DNS cache.
-
Download the DNS-Flush tool and save the file to your Desktop.
-
Navigate to your Desktop, extract or open Flush DNS.zip and double-click Flush DNS.exe (if prompted to continue, click Yes). The tool will automatically flush and register your DNS cache.
-
After your computer restarts, open your ESET product and run a Computer scan.
The Computer scan should finish without detecting an infection. If no threat is detected, no further action is needed.
Still experiencing an issue? Need further assistance? Contact ESET Technical Support.