Issue
- Your ESET product displays the notification "Detected covert channel exploit in ICMP packet"
- Games or other applications that connect to the internet do not function properly when this notification is displayed
Details
If you receive a “Detected covert channel exploit in ICMP packet” message from your ESET product in your notification area, traffic to or from your computer is being blocked by ESET’s active defense system. Fragmented ICMP packets may be used to enable rapid detection of a client connection to the domain controller. In some cases, this detection can prevent games or other applications that connect to the internet from working as expected.
Solution
If you are unsure that the notifications you are receiving are from a legitimate threat, disable notifications after attack detection. You will stop receving threat notifications without lowering your level of protection.
If you are having an issue that is preventing a network-enabled application or game from functioning properly, we recommend that you create an IDS exception for the application to stop further notifications from being sent. Always make sure that your Personal firewall module is up-to-date. Check my firewall version.
Disable notifications after attack detection
Disable notifications and configure your ESET product to run in the background without lowering your level of protection if you are unsure that the cause of the notifications is a legitimate threat:
- Press the F5 key to access Advanced setup.
- Click Firewall and expand Advanced → IDS and Advanced Options.
Version 9.x: Click Personal Firewall and then click Edit next to IDS and advanced options in the Basic section.
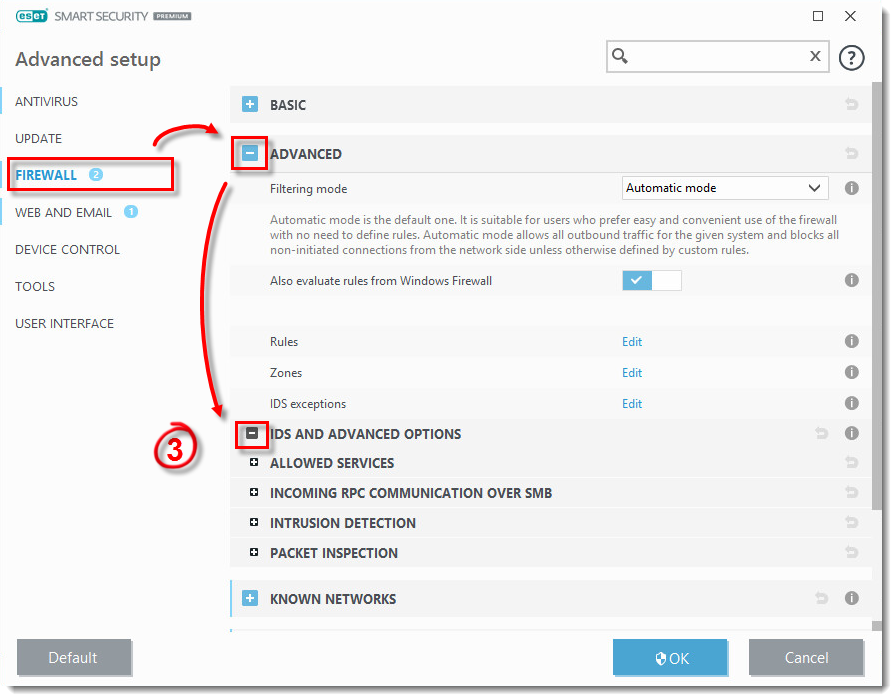
Figure 1-1
- Expand Intrusion Detection and click the toggle next to Display notification after attack detection to disable it. Click OK twice to save your changes and exit Advanced setup.
You should no longer receive "Detected covert channel exploit in ICMP packet" notifications.
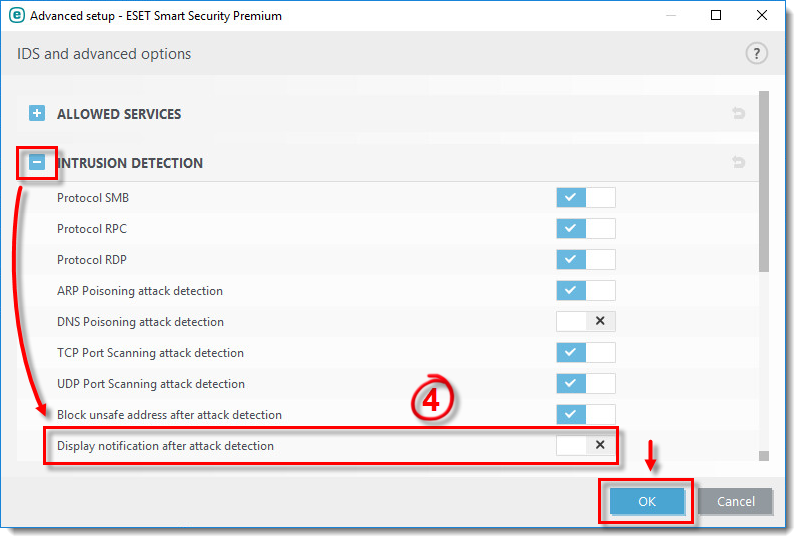
Figure 1-2